Invented by LI; Xun, VIGILANT; David, THALES DIS FRANCE SAS
Today, digital devices use secrets like private keys to keep our data safe. But attackers are getting smarter, using things like deep learning to guess these secrets by simply watching how a device acts, such as how much power it uses or how long it takes to run. Let’s talk about a new invention designed to keep these secrets safe, even from the most clever attacks. We’ll explore why this matters, how things worked before, and how this new approach changes the game.

Background and Market Context
In our digital world, security is everything. Whether you use a smart card to pay for groceries, log in to your bank, or send a private message, your device uses cryptography. This is a way of locking information so that only people with the right key can open it. But it’s not just about having tough locks; it’s also about hiding the key from anyone who might be watching.
Attackers have found ways to peek at devices without breaking the lock itself. Instead, they watch for clues—like how much power a chip uses, or how long it takes to do math. These clues, called “side channels,” can reveal the secret key if analyzed carefully. This kind of attack is called a side-channel attack (SCA), and it’s a real threat to banks, smart cards, phones, and even cloud computers.
What’s changed recently is the use of deep learning, a smart type of computer program that can spot hidden patterns in huge piles of data. Attackers feed these programs lots of side-channel information and teach them to guess the secret key. Deep-learning side-channel attacks (DL-SCA) are now a top danger. They work well even if you try to mix things up or add some noise. Standard tricks, like adding delays or shuffling data, are no longer enough to stop them.
All devices that use public key cryptography, like RSA or ECC, are at risk. These are the systems that let us sign documents, make secure connections, and encrypt data. If someone gets your private key, they can pretend to be you or read your secrets. So, defending against DL-SCA is more important than ever, especially as these attacks become easier and more common.
The need for stronger protection is clear. Big industries—finance, identity, health, and IoT—are looking for real solutions. Certification labs are testing devices with deep-learning attacks. If a device can’t pass, it can’t be sold in many markets.
Scientific Rationale and Prior Art
Let’s understand how these attacks work and why old defenses are not good enough. In the past, side-channel attacks looked for patterns in timing, power, or even sound. Attackers would try to match what they saw to what they guessed was happening inside the device, such as when it was multiplying numbers or handling key bits.
To fight back, device makers used tricks like:
– Adding random delays, so the timing changes each time
– Mixing up where data is stored, so it’s harder to track
– Making dummy operations, so it’s not clear when real math happens
These are called countermeasures. They work okay against simple attacks, but deep learning is much smarter. It doesn’t care if the data is mixed up or delayed. It looks at the big picture and finds tiny clues in the noise, learning how to map what it sees to the key bits.
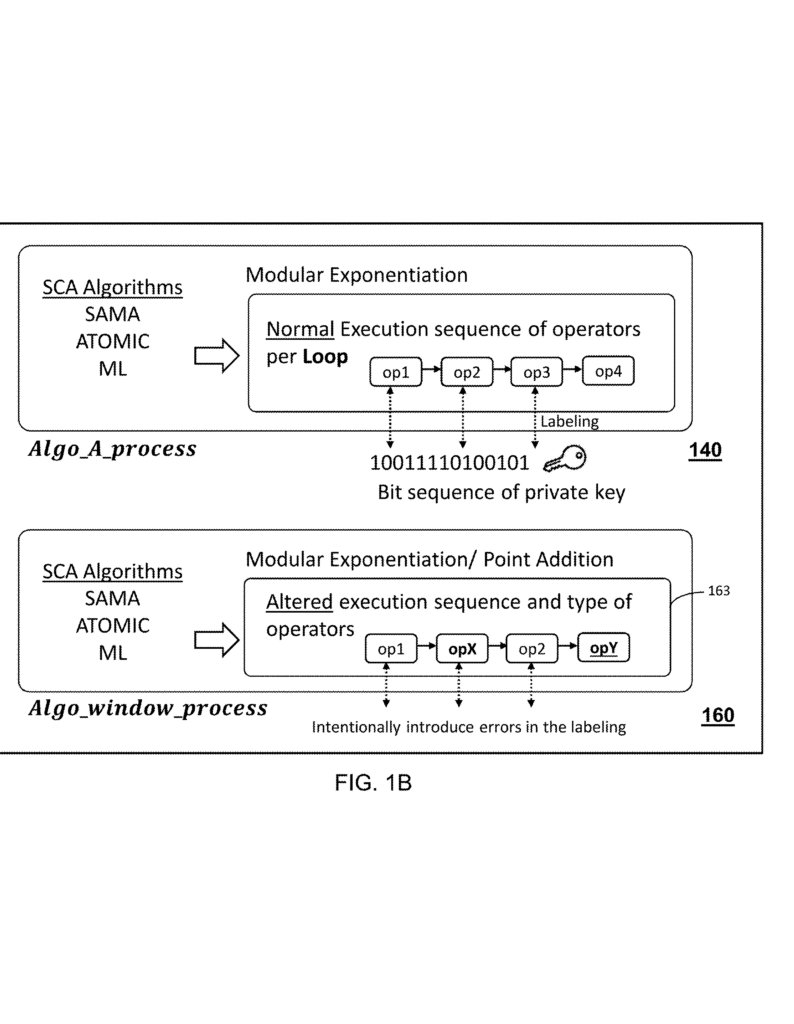
Public key algorithms, like RSA (which uses modular exponentiation) and ECC (which uses point multiplication), are especially at risk. The math is done in steps, where each bit of the secret key changes what happens. Deep-learning models can watch these steps over and over, learning which step matches which key bit. If the model is trained with the right labels, it can predict the key with scary accuracy.
Older defenses just can’t keep up. For example, “Square and Multiply Always” (SAMA) tries to do the same operations for every key bit, so it looks the same whether the bit is a 0 or a 1. But deep learning can still spot subtle differences. Even when algorithms try to be “atomic,” always doing the same thing, there are often leaks in how data is handled or stored.
Some tried to stop the deep-learning model from being trained correctly. They added more noise or mixed things up inside the device. But these changes only slowed attackers down—they didn’t stop them. As deep learning tools get better, the problem gets worse.
So, what’s needed? A way to break the link between what the model sees (the side-channel data) and the real key bits. If the model can’t learn the right mapping, it can’t guess the key. This is what the new invention does—it aims to confuse the deep-learning model by randomizing the connection between operations and key bits, making the attack fail before it even starts.
Invention Description and Key Innovations
This invention brings a new way to protect cryptographic algorithms—especially those used in RSA and ECC—from deep-learning side-channel attacks. The idea is simple at its core: make it so that attackers can’t easily label the side-channel data with the right key bits, no matter how smart their learning model is.

Here’s how it works, step by step, in easy words:
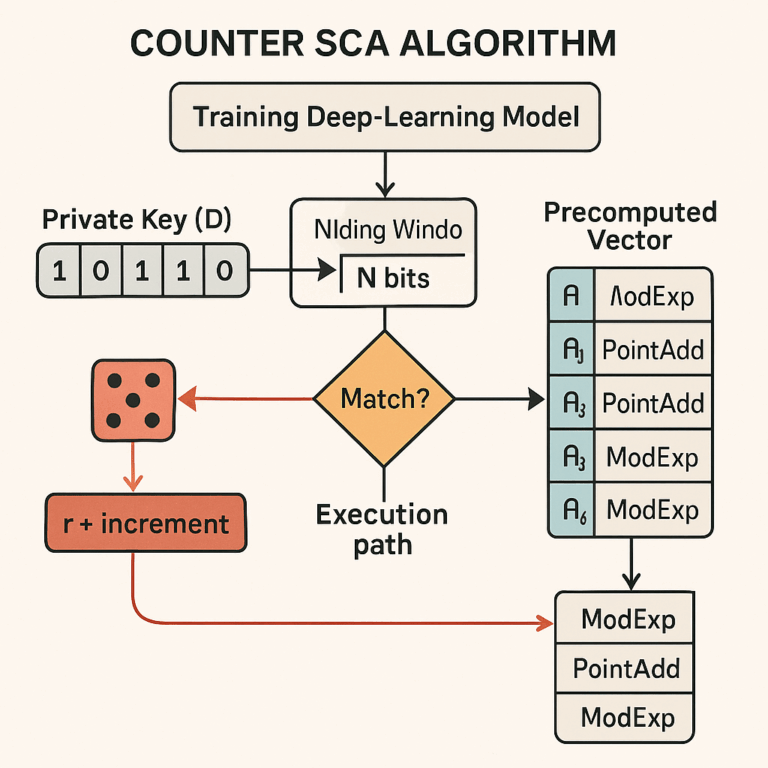
Mixing Up the Operations
The invention changes how the device handles the secret key during important math operations. It uses something called a windowing process. Instead of handling one bit at a time, it looks at small groups of bits (a “window” of size N). This is not new by itself, but here’s the twist: for each group, the device makes a random choice about how to process it, using a random number.
For each window, the device decides if it will do things in the normal way or in a special, altered way. This decision is based on whether the group of key bits matches the chosen random number (plus a small offset). If it matches, the device pulls a value from a secret, precomputed list (a vector) and uses it in the operation. If it doesn’t match, it acts normal. This choice is made for every window of key bits, so the exact pattern changes every time.
Precomputed Vectors
To make this work, the device sets up a set of values before starting (the precomputed vector). For RSA, this is a set of multiplications; for ECC, it’s a set of point additions. These are indexed by the random number, so only the device knows which one is being used each time. This means that even if an attacker watches closely, they don’t know which precomputed value is being used at which step.
Randomness at Every Step
The random number can be picked once at the start, or freshly for each window. This makes the pattern of operations change all the time. The window size (N) can also be chosen based on how much protection is needed and how much memory the device has. Bigger windows mean more possible patterns and more confusion for attackers.
Breaking the Learning Process
The deep-learning attacker needs to label each operation with the correct key bits to train their model. But with this invention, the pattern of operations no longer matches the key bits in any fixed way. Sometimes, an operation comes from the normal process; sometimes, it’s from the special process using the precomputed vector. Since the attacker doesn’t know the random number or which value was used, they can’t label the data correctly.
This leads to lots of errors in the training phase. The model is fed wrong labels over and over. When the attacker tries to use the model to guess the key, it fails badly. The more windows and randomness, the more errors, making the model useless for attacks.
Works with Many Algorithms
This method isn’t just for one algorithm. It works with different types of safe algorithms for RSA and ECC, like SAMA, ATOMIC, and Montgomery Ladder. Each of these can use the windowed mixing process to break the link between operations and key bits. For ECC, the same idea applies, just using point additions instead of multiplications.
Same Performance, Stronger Security
Importantly, this approach doesn’t slow down the device. The number of operations stays the same as before; only the pattern changes. The device might need a little more memory to store the precomputed values, but this is small compared to the gain in security. There’s no need for extra hardware or complicated timing tricks.
Flexible and Adaptable
The invention lets device makers choose the window size and how often to change the random number. They can balance between memory use and security level. Even if attackers know the method is being used, they can’t predict the random choices inside the device.
Defending Against Many Attacks
This approach helps against not just deep-learning attacks, but also timing attacks, power-monitoring attacks, and other side-channel threats. By making the operation patterns unpredictable and unlinkable to key bits, it closes off many paths attackers use to steal secrets.
How It Looks in Practice
Imagine a smart card using RSA to sign a message. Normally, each step in the signature process matches a key bit. An attacker records the power use and tries to teach a deep-learning model to spot when a key bit is 1 or 0. With this invention, sometimes the card does a normal step, and sometimes it does a step using a secret precomputed value, chosen at random. The attacker sees power use, but can’t tell which is which. Their model gets confused, and the key stays safe.
Or think of an IoT device using ECC to encrypt data. The same idea applies. The attacker can’t label the steps correctly, so their model can’t learn the key.
Easy to Add to Existing Devices
The method can be added in software or firmware to most devices. There’s no need to change the hardware. This makes it easy for makers of smart cards, secure elements, and other products to upgrade their defenses without redesigning everything.
Ready for Real-World Use
The invention is designed to work on all kinds of devices—processors, crypto-processors, smart cards, and secure elements. It can be part of the system that runs the cryptographic algorithms, protecting them at the very core.
Summary of the Steps
1. Pick a window size (N bits).
2. Precompute a set of values (multiplications for RSA, additions for ECC).
3. For each window in the secret key, pick a random number (either once or each time).
4. If the key bits match the random number (plus an offset), use the special value from the precomputed set; else, do the normal step.
5. Repeat for all windows in the key.
This randomization and mixing make it impossible for attackers to label the side-channel data correctly, stopping deep-learning attacks before they can begin.
Conclusion
Side-channel attacks are a real and growing threat, especially as deep learning gets better at finding secret keys from physical clues. Old ways of defending are not strong enough. This invention brings a simple but powerful method: mix up the patterns attackers rely on, using random choices and precomputed values. This breaks the link between what the attacker sees and what really happens inside the device, making deep-learning models fail.
The method is flexible, works with common cryptographic algorithms, and can be added to many types of devices without loss of speed or need for new hardware. For anyone making or using secure devices, this approach gives a strong new shield against today’s most advanced attacks. As more devices connect to the internet and handle important secrets, using such protection will be key to keeping our digital world safe.
Click here https://ppubs.uspto.gov/pubwebapp/ and search 20250233732.
