Invented by WANG; Su, LU; Fang, MAI; Yufei
This article will help you understand a new patent for making remote attestation easier in database systems. We’ll break it down into three main sections. By the end, you will know why this invention matters, what was done before, and what makes this solution new and helpful.
Background and Market Context
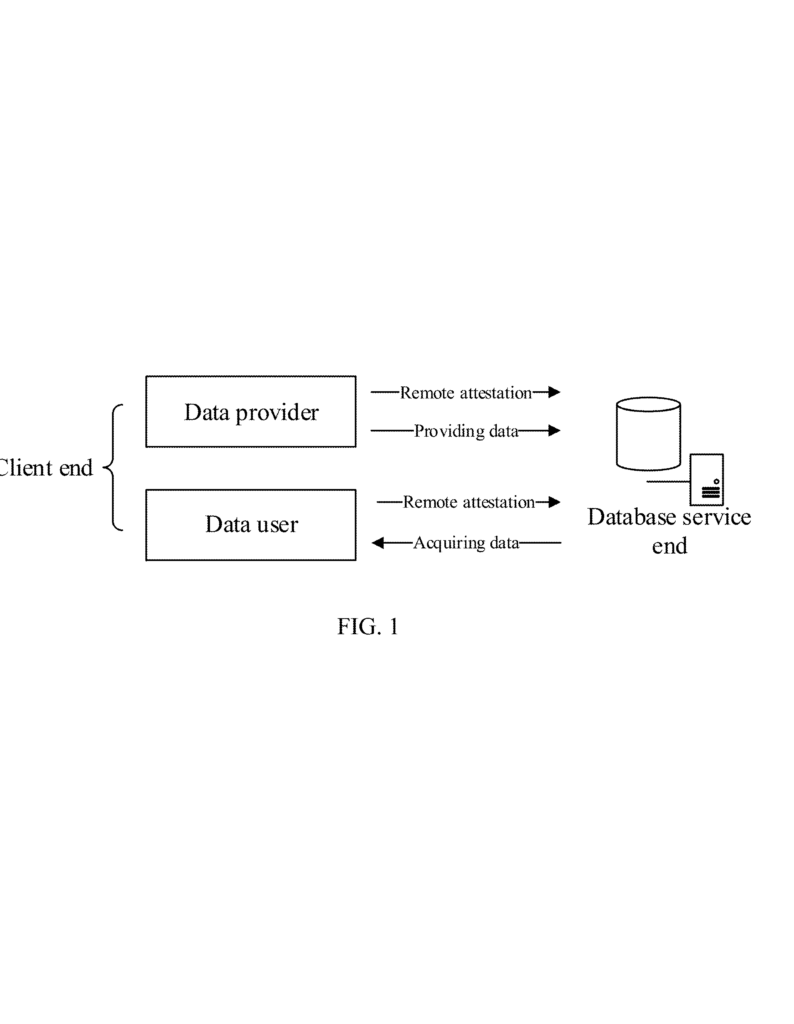
Imagine you store your most precious secrets—like your favorite recipe or a list of family birthdays—on someone else’s computer. You want to be sure no one can peek at them. In the world of cloud computing, this is what millions of people and companies do every day. They trust third-party computers, called servers, to keep their important information safe.
But how do you know the server is truly safe? How do you make sure no one has secretly changed the computer or installed bad software that could steal your secrets? This is where remote attestation comes in. It works like a digital lock-and-key handshake: you ask the server to prove it is safe, and it gives you a special report showing its safety status. If you trust the report, you can safely share your secrets.
Cloud computing is everywhere now. Big companies, hospitals, banks, and even schools use it for everything from storing files to running huge databases. These databases need to be safe, especially when they handle private or sensitive data. The problem is, checking if a remote database is safe is not easy. It often requires special tools and deep technical knowledge. Developers have to use complex kits called SDKs (software development kits) and write code in tricky languages like C or C++. This slows down progress and makes security harder to use for most people.
As more businesses move their data to the cloud, the need for simple, reliable, and trustworthy attestation grows. Everyone—from small startups to large enterprises—wants a way to easily check if their data is truly secure, without needing a team of security experts.
Scientific Rationale and Prior Art
Let’s look at how remote attestation works and what has been done before. The main idea is that you want to check if a computer is running trusted software in a protected space. Trusted Execution Environments, or TEEs, are special areas inside a computer’s brain (the processor) where data and code can run safely, away from prying eyes. TEEs create a zone where only approved programs can see the data, like a secret clubhouse with a locked door.
To check if this secret clubhouse is still safe, remote attestation is used. It is like asking the clubhouse to show proof that its door is still locked and only trusted members are inside. The clubhouse prepares a report, signs it, and sends it to you. You can then check the report to decide if you want to let your secrets inside.
Before this invention, most remote attestation tools were hard to use. They needed you to use a special SDK, often provided by the hardware company that makes the TEE (like Intel or AMD). You had to write low-level code, often in C or C++, and use special commands that changed from one hardware platform to another. Each TEE had its own way of doing things, which made life difficult for developers and companies who wanted to use different types of hardware or move between cloud providers.
Databases, which are the heart of most business software, made things even harder. If you wanted to check that a database was running in a safe TEE, you had to write special programs just to talk to the TEE’s SDK. These programs were not easy to build or change. There was no simple way for a database user—who might only know how to use SQL (the common language for databases)—to ask for an attestation report or check if the report was valid. Everything was hidden behind layers of programming and technical hurdles.
Developers faced a big problem: every time they wanted to use remote attestation, they had to dig into the SDK, learn new commands, and write lots of code. This took time. It also made it hard to update or debug the attestation process. If something went wrong, you had to fix low-level code and maybe even recompile everything. This made remote attestation a tool for experts, not for everyday users or developers who just wanted to keep their databases safe.
People tried to make things easier by building wrappers—extra layers that hide the complexity—but these were still tied to specific programming languages or hardware. Nothing existed that let a database user simply use an SQL command to get or check an attestation report, no matter what hardware or SDK was running under the hood.
Invention Description and Key Innovations
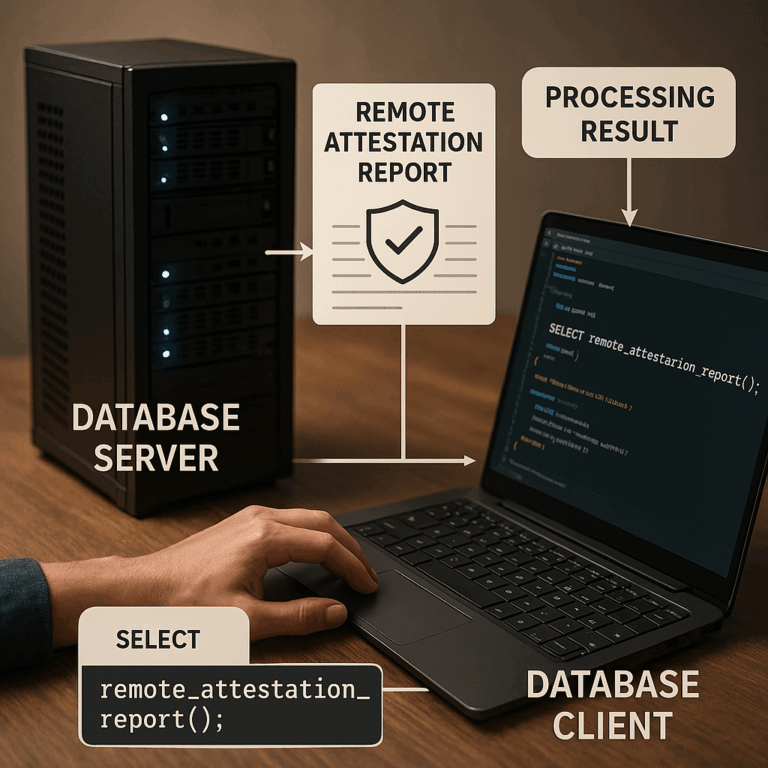
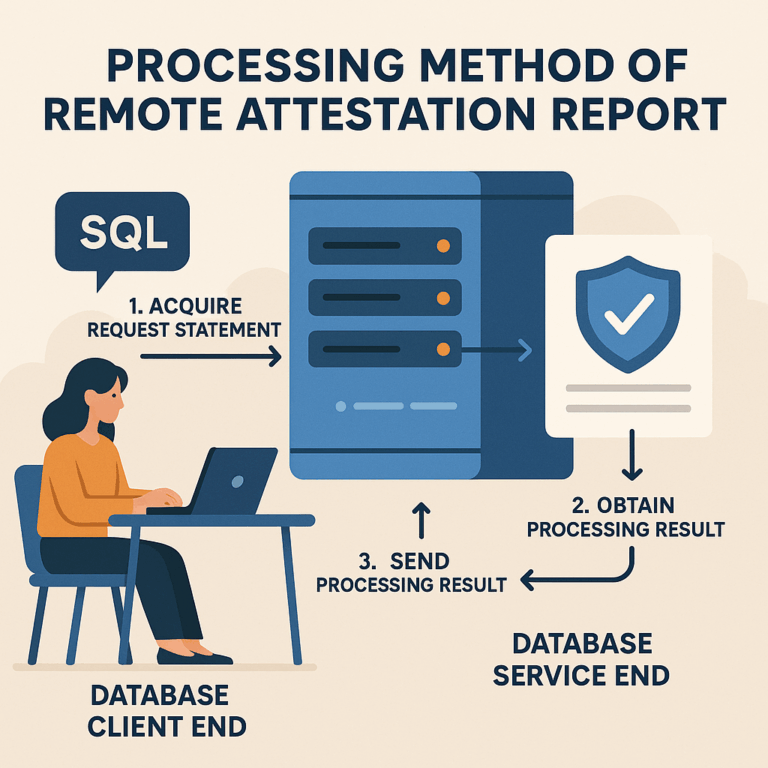
This patent changes everything by making remote attestation as simple as sending a normal SQL command to your database. Here’s how it works, in easy words:
The inventors created a way for database users to ask for or check attestation reports using the same language they already know: SQL. Instead of writing complex code or calling special SDKs directly, users can just type a simple SQL command. The system does the hard work behind the scenes.
At the heart of this invention is a smart extension for the database. This extension acts like an interpreter. When the database receives a special request (like “give me an attestation report” or “check this report”), the extension knows which function to run. It calls the right part of the TEE’s SDK, gets the result, and sends it back to the user, all without the user needing to know any details about the SDK or the hardware.
Let’s use an example. Suppose you are using a PostgreSQL or SQLite database. In the new system, you can run a command like:
SELECT RaQuoteGenerate(challengeNumber) as Report;
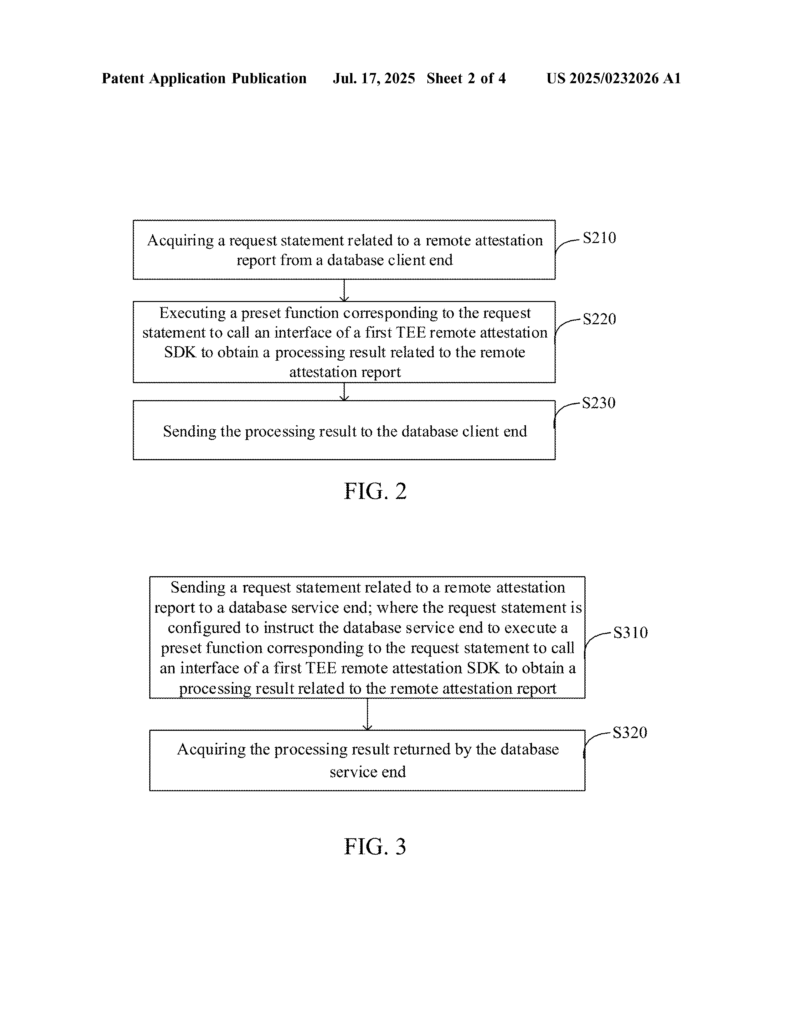
This command tells the database, “Please use the attestation generation function and give me a report.” The database’s extension takes this command, calls the TEE’s SDK, generates the attestation report (which describes the security and setup of the database’s execution environment), and returns the report to you. You can store it, share it, or use it however you want.
If you want to check if a report is valid, you can run:
SELECT RaQuoteVerify(ra_report) as VerificationResult;
The system checks the report using the SDK and tells you if it passes (for example, a result of 0 means success, anything else means something is wrong).
This approach has several key innovations:
First, it hides the messy details of the SDK and the hardware. Users only need to know SQL. The extension takes care of talking to the TEE, no matter if it’s Intel SGX, AMD SEV, ARM TrustZone, or something else.
Second, it allows for online editing, testing, and updating. Since SQL is an interpreted language, you don’t need to recompile anything. If you want to change how you get or check attestation reports, you can simply update your SQL commands or the extension’s logic. This makes development much faster and easier.
Third, it introduces a new data type for storing attestation reports in the database. For PostgreSQL, the report is stored as BYTEA (a byte array). For SQLite, it’s stored as BLOB (a binary data block). This makes it easy to save, export, and move reports between systems, and even lets other programs analyze or verify them if needed.
Fourth, it is flexible about where verification happens. You can check the attestation report in the database service itself, or you can take the report and verify it in your own client using your own tools or the hardware vendor’s SDK. This gives users more choice and control.
Fifth, it is future-proof. Because the extension can call any TEE SDK’s interface, it works with current and future hardware. As new types of TEEs or attestation methods appear, the system can be updated to support them without changing how users interact with it.
This invention is not just for experts. It brings strong security to everyone using a database, making remote attestation as easy as running a normal query. Developers can now add attestation to their applications without learning new tools or programming languages. Businesses can check the safety of their databases quickly and reliably. The whole process is smoother, safer, and much easier to use.
Conclusion
Remote attestation is a vital tool for keeping cloud databases safe, but until now, it was too hard for most people to use. This patent solves that by letting users call attestation functions straight from their database using simple SQL commands. By hiding the tricky parts of TEEs and SDKs, making attestation flexible, and allowing reports to be easily stored and checked, this invention makes real security available to everyone. In a world where data safety matters more every day, this simple but powerful approach is a game-changer for cloud computing and database security.
Click here https://ppubs.uspto.gov/pubwebapp/ and search 20250232026.
