Trade secrets are often the most valuable thing a deep tech team owns in the first two years.
Not the pitch deck. Not the logo. Not even the first version of the product.
It is the “how.”
How your model is trained. How your robot plans motion in messy spaces. How you cut power use by 40%. How you get signal from noisy data. How you make a chip behave. How you make the system work in the real world, not just in a lab.
And here is the hard truth: most startups lose trade secrets in boring, quiet ways. Not through a movie-style hack. They lose them through a contractor. A loose Slack message. A shared Google Drive link. A demo with too much detail. A new hire who is excited and posts the wrong thing on LinkedIn. A partner call where someone says, “Sure, I can explain the core trick.”
Trade secret protection is not a legal document you sign once. It is a set of daily habits. Real processes. The kind your team can follow even when you are tired, busy, and shipping fast.
This guide is about those processes.
It is written for founders building robotics, AI, and other deep tech products who want protection that actually holds up when it matters—during a funding round, during due diligence, during a partnership deal, or when a competitor tries to copy you.
At Tran.vc, we work with technical teams early to turn real invention into real leverage. Sometimes that is patents. Often it is a smart mix: patent what should be public, and keep the rest as trade secrets with clean controls. If you want help setting up that plan from day one, you can apply anytime here: https://www.tran.vc/apply-now-form/
Now, before we go deep, let’s get one thing clear.
A trade secret is not “something you do not tell people.” That is too vague to protect you.
A trade secret is information that:
- gives you a real business edge because others do not know it, and
- you actively protect with reasonable steps.
That second part is where most teams fail. They have the secret. They do not have the steps.
So the goal is simple: build a small system that makes it easy to protect secrets without slowing down the team.
Let’s start with the foundation: how to decide what is actually a trade secret in a deep tech startup.
In deep tech, founders often label everything as secret. That feels safe, but it is not useful. If everything is secret, then nothing is treated with special care. People get numb. Files spread. Access grows. Then one day you cannot prove you ever protected the thing you claim is secret.
Instead, you want to be sharp. You want a clear line between:
- what is public or will be public soon,
- what is internal but not critical,
- and what is truly a trade secret.
Think of it like a lab. You do not lock every drawer. You lock the drawer with the rare material.
Here is a practical way to do it without long meetings.
Pick three buckets:
Bucket A: Crown jewels (true trade secrets).
These are the small number of things that, if copied, would let a smart team catch up fast. In robotics, this could be your motion planning trick, your calibration method, your data pipeline that makes training stable, your safety logic, your control loop tuning process, your custom dataset labels, your special sensor fusion approach. In AI, it could be a training recipe, a filtering step, a scoring function, a system prompt structure, a way you reduce hallucination, a retrieval setup that makes accuracy jump, a unique synthetic data generator, or a deployment method that cuts cost.
Bucket B: Important internal know-how.
Valuable, but not the core edge. Examples: standard coding patterns, internal tools, team docs, basic scripts, product specs. You protect these, but you do not treat them like gold.
Bucket C: Public or soon-to-be public.
Marketing pages, published papers, open docs, open source parts, talks, demos you plan to show.
The key is to keep Bucket A small. Ten items is already a lot for an early team. Many startups can start with five.
You might ask, “What if we miss something?” You will not. Because this is not a one-time task. You update it when the product changes.
Now comes the part that makes trade secrets real: you must be able to point to a process and say, “We treated Bucket A differently, from day one.”
That process has four pillars:
- how you label and store secrets,
- how you control access,
- how you handle people (hires, exits, contractors),
- and how you handle sharing (investors, partners, demos).
If you only do one pillar, you are exposed. You need all four, but you can do them in a simple way.
Let’s talk about labeling and storage first, because it is the easiest win and it sets the tone.
Most teams store the most sensitive work in random places:
- a founder’s laptop,
- a personal Google Drive,
- a shared Notion space with open access,
- a GitHub repo where every contractor is a collaborator,
- a Slack channel with screenshots and key details,
- a folder called “secret stuff” that is shared with half the company.
This is not protection. This is hope.
Protection means you can answer these questions fast:
- Where are the crown jewels stored?
- Who has access right now?
- Who granted that access?
- What happens when someone leaves?
- Can we show an investor we had controls in place?
A clean baseline process looks like this:
Your trade secrets live in a dedicated place with clear rules. That place can be a private Git repo, a locked folder, or a secured doc space. The tool matters less than the discipline.
The discipline is:
- Every crown jewel doc has a simple label at the top: “CONFIDENTIAL — TRADE SECRET.”
- Every file name includes a short marker, like “TS-” at the start.
- Every crown jewel item has an “owner” inside the company. One person who is responsible for keeping it clean.
- Every crown jewel item has a short “why it matters” note. Two sentences. This sounds small, but it helps a lot when you are busy and someone asks, “Can I share this?”
That last piece is important. People protect what they understand. If your team knows why something is sensitive, they will treat it with care.
Now, storage is not only “where the file sits.” It is also how it moves.
A deep tech team will move secrets through:
- Slack,
- email,
- screen shares,
- demo videos,
- notebooks,
- tickets,
- and quick Loom recordings.
If you ignore these paths, your storage plan is a paper shield.
So you want one rule that is easy to follow:
Crown jewels do not go into casual tools.
That means: do not paste the full training recipe in Slack. Do not drop the core algorithm in a Jira ticket. Do not attach a key diagram to an email thread with ten people.
Instead, you link to the secure source. Or you share a short summary that is safe.
This is where founders often push back: “But we move fast. We cannot slow down.”
You do not have to slow down. You just need a small habit: link, do not paste.
The difference is huge.
If you paste into Slack, you lose track. If you link to a controlled doc, you keep one source of truth, access is logged, and you can remove access later.
Now let’s get tactical in a way that founders actually use.
If you want trade secret processes that work, you need a simple “secret map.” Not a 30-page policy. A one-page map.
This map has:
- the list of crown jewels (five to ten),
- where each one is stored,
- who owns it,
- who has access,
- and what the safe “share version” is (if any).
A “share version” is a redacted explanation you can use for investor calls, partner talks, or recruiting, without giving away the trick. Many founders struggle with this. They either share too much, or they share nothing and sound vague. A share version helps you stay confident.
Example: instead of sharing the exact motion planning heuristic, you say, “We use a hybrid approach that blends model-based planning with learned constraints, which lets us keep safety strong while staying fast.” That gives a clear story without handing over the recipe.
When Tran.vc works with teams, we often help build this map alongside patent strategy, because the two work together. Some inventions should be patented early because they are easy to reverse engineer once shipped. Others should stay secret because they are hard to detect from the outside and would stay valuable for years. That mix is where leverage comes from. If you want help with that mix, you can apply here: https://www.tran.vc/apply-now-form/
Now, one more point before we move to access control.
Trade secret protection is not only about stopping theft. It is about making your company fundable.
Serious investors ask questions like:
- What is defensible here?
- What happens if a big company copies you?
- Do you own the work your contractors did?
- What controls do you have around code and data?
- Is the IP clean?
If you can say, calmly, “We have a trade secret map, access controls, and clean onboarding/offboarding,” you sound like a team that can scale.
If you say, “We keep it secret,” you sound like a team that will get surprised later.
Access Control That Does Not Kill Speed
The goal: fewer doors, better locks
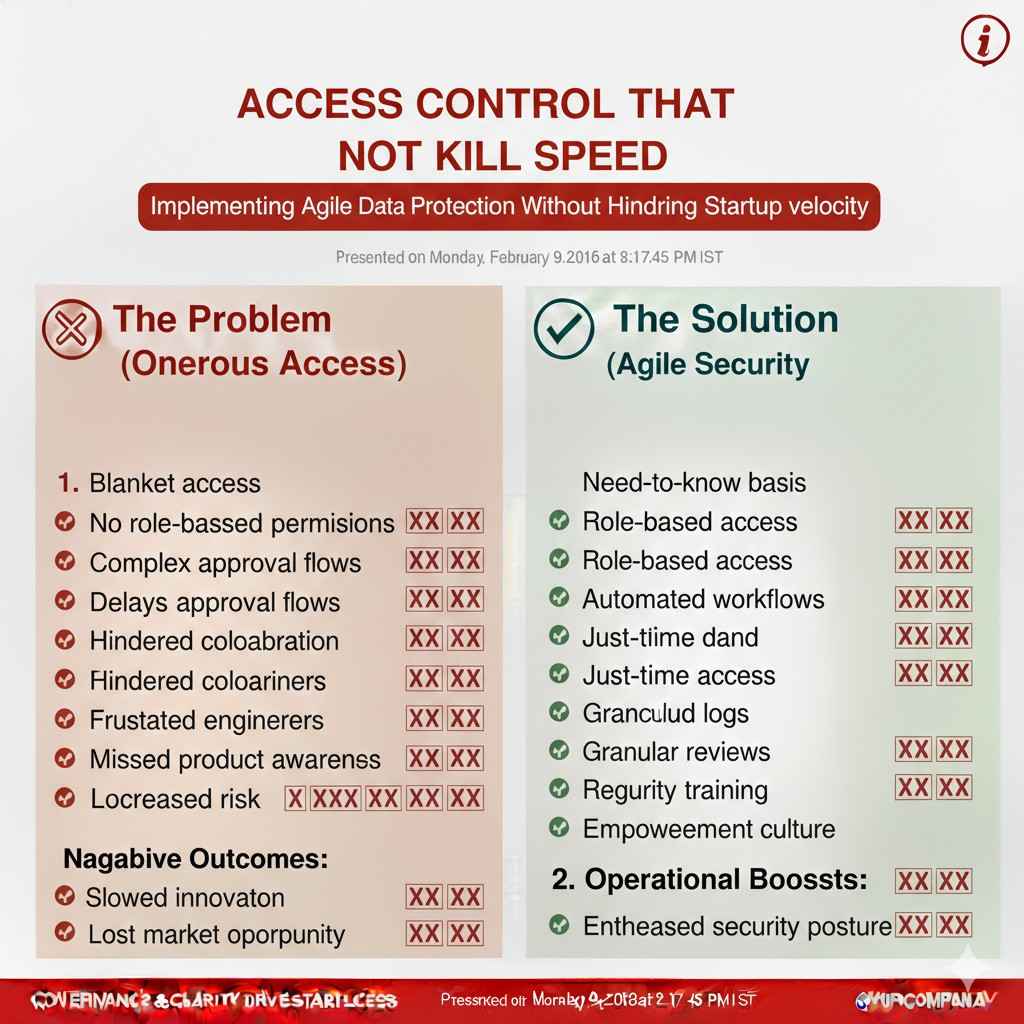
Access control sounds like a big-company problem, but in a startup it is the fastest way to lose a trade secret without noticing.
If a contractor has access to your full repo, your full dataset, and your full roadmap, you do not have “trust.” You have a single point of failure.
The aim is not to lock everything down. The aim is to make sure only the right people can reach the crown jewels, and only when they truly need it.
A simple rule deep tech teams can follow
In early-stage deep tech, the safest rule is “need to know, not nice to have.”
That means people get access when their task requires it, not because it might help someday. It also means access is removed when the task ends, not when someone remembers months later.
This is not a lack of trust. It is a professional standard that protects everyone, including your team.
Separate your crown jewels from the rest

Most leaks happen because the crown jewels live inside the “main” repo or the “main” drive.
When everything is mixed together, you cannot share work without sharing secrets. That is when people start forwarding folders, adding users, and granting broad access to keep moving.
A better setup is to split work into two zones: a general zone where most building happens, and a restricted zone where the crown jewels live.
The two-zone model in plain terms
Your general zone contains day-to-day code, product docs, and normal engineering notes.
Your restricted zone contains only the true trade secrets: the special training recipe, the key dataset labels, the unique test harness, the sensitive calibration procedure, or the private scoring logic that makes results strong.
This split is powerful because it changes the default behavior.
When someone asks for access, you are no longer deciding “Can they see everything?” You are deciding “Do they need the restricted zone, or not?”
Why deep tech needs this more than most startups
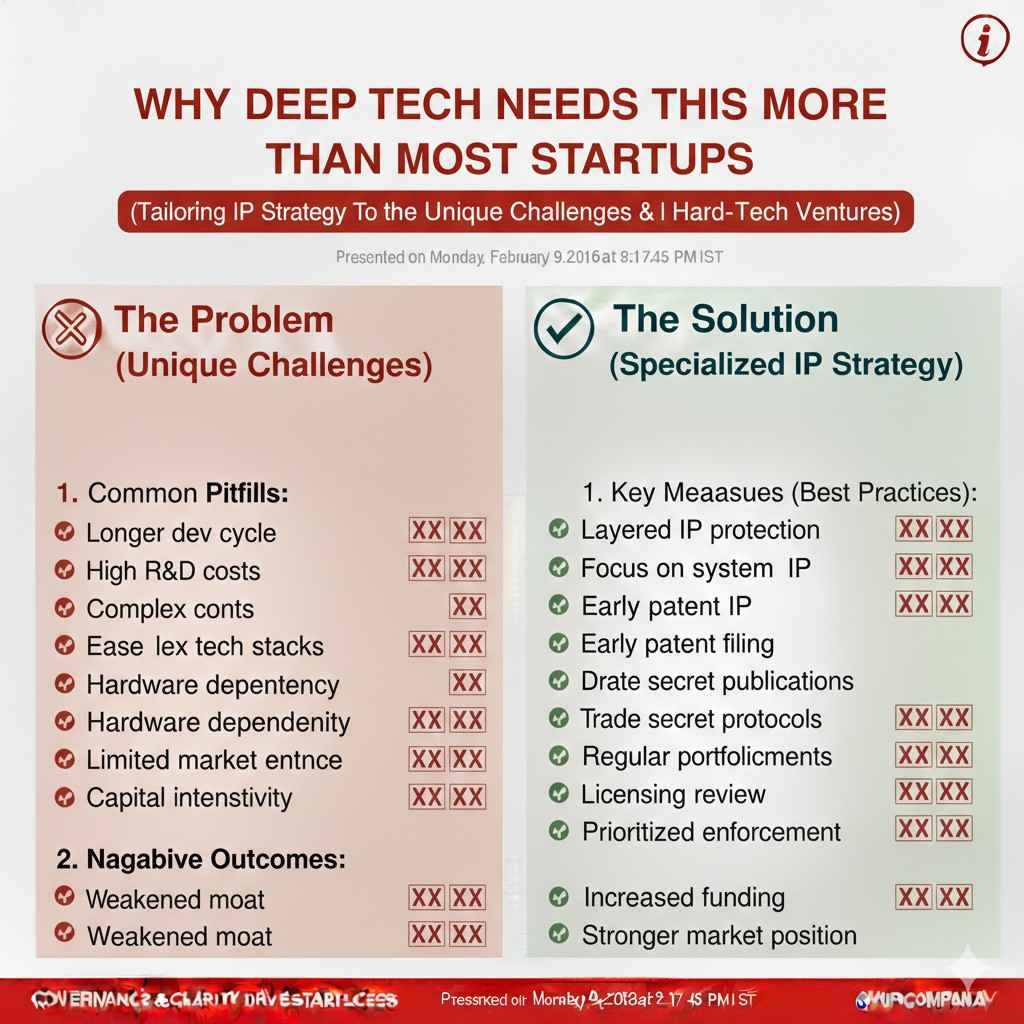
Deep tech secrets are often in the “process,” not just the “idea.”
The process usually touches code, data, and testing. A single engineer who sees all three can re-create your edge faster than you think.
When you separate the restricted zone, you make it harder for any one person to walk away with the full recipe.
Control access to data like it is your product
In AI and robotics, the dataset is often the moat.
Yet teams regularly share datasets through a link that gets copied and re-shared, or stored on a personal drive because it is “easier.”
That is not protection. It is risk.
Treat your sensitive data as its own asset with its own access rules, separate from the rest of your files.
Keep a clear record of who can access what
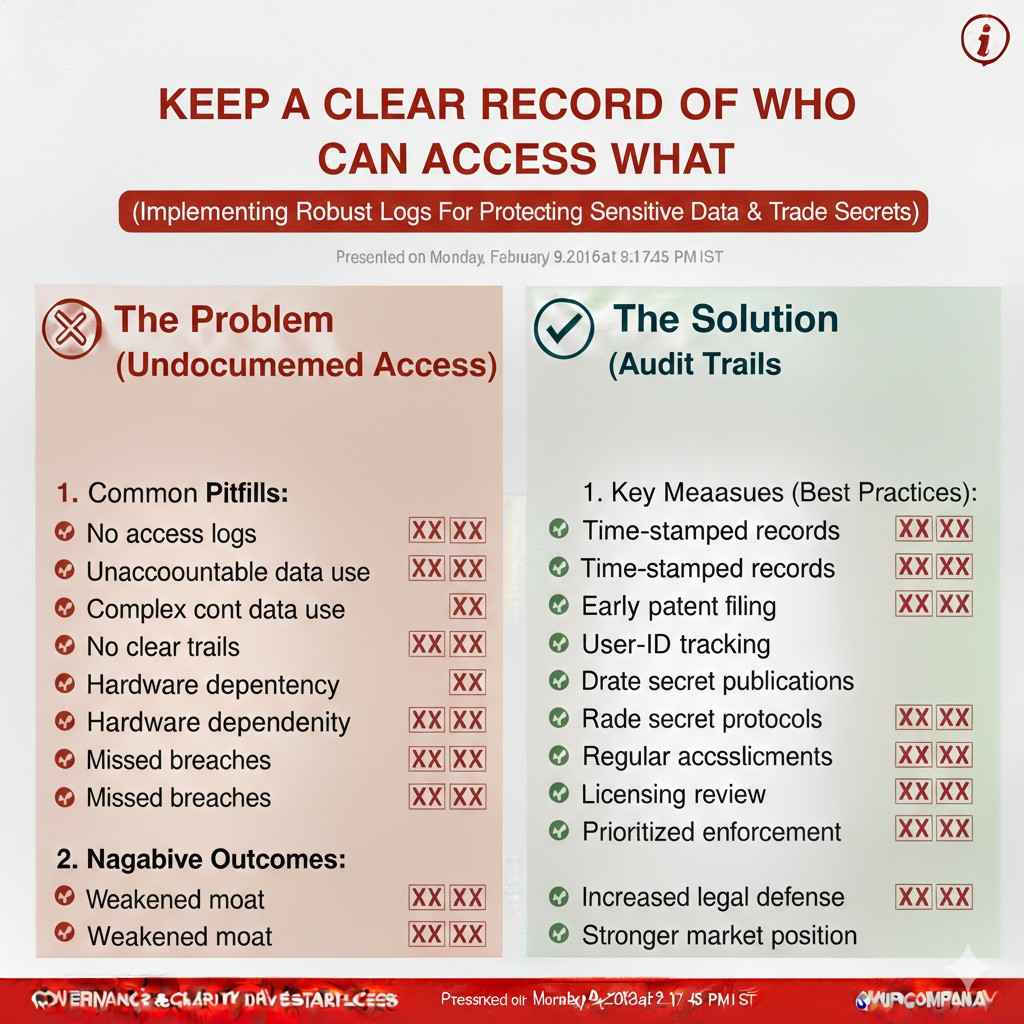
One of the biggest trade secret failures is simple: you cannot prove you protected the secret.
If you ever need to enforce your rights, you will be asked what steps you took to keep it secret.
So you want a system that shows access decisions were real. Not informal. Not vague.
The simplest way is to keep access lists short and review them on a schedule you can actually follow.
The monthly access check that takes fifteen minutes
Once a month, a founder or tech lead opens the trade secret map and checks who has access to each crown jewel item.
If someone no longer needs access, remove it that day. If someone new needs access, add it with a clear reason and a clear end date.
This is not busy work. It is the kind of small habit that keeps you safe when the company gets bigger and messier.
Contractors are the fastest path to accidental loss
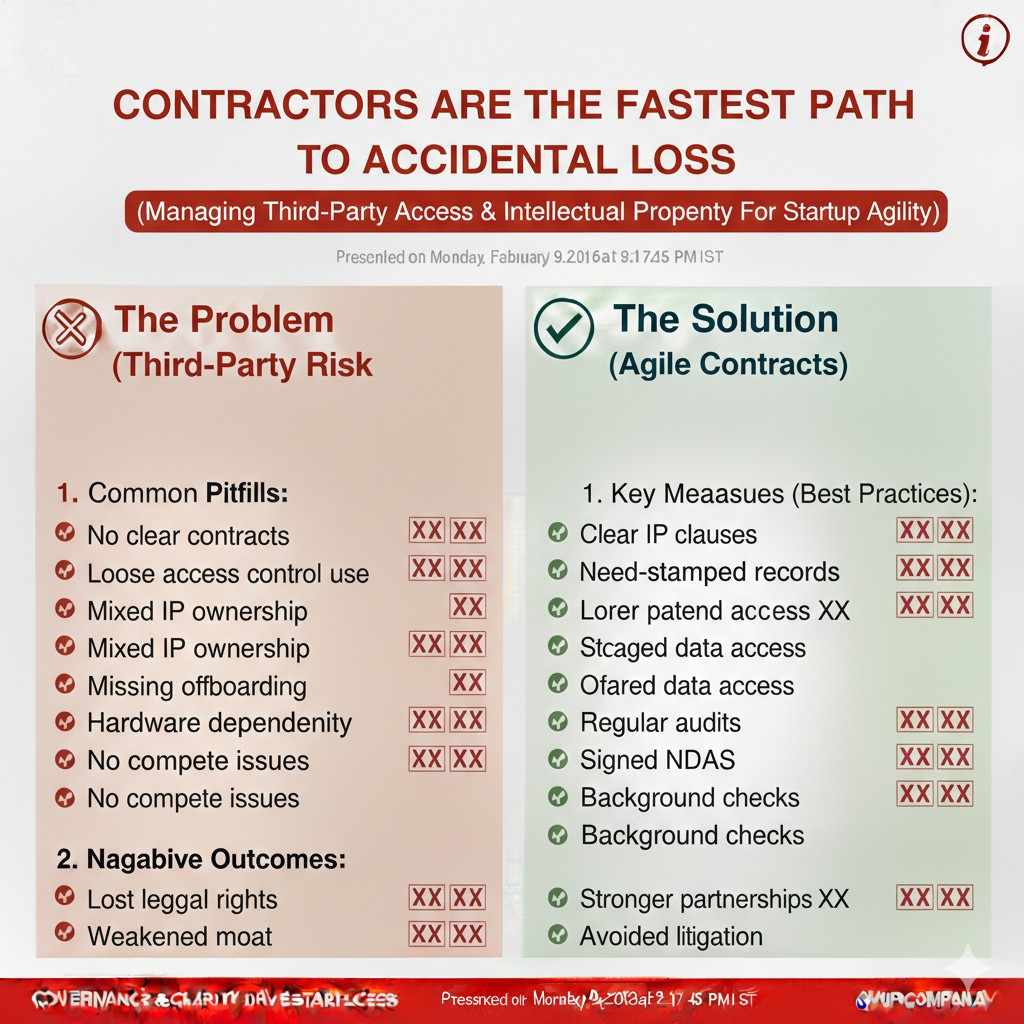
Contractors can be a great force multiplier, but they are also the most common source of trade secret leakage.
Not because they are bad people. Because they work across many clients and many systems, and they often reuse patterns, tools, and habits.
If you give a contractor wide access, you are betting your core edge on perfect behavior. That is not a smart bet.
Give contractors “task access,” not “company access”
A contractor should get only what they need to deliver a clear task.
If they are building a UI, they do not need the training recipe. If they are cleaning data, they do not need the full model weights. If they are writing firmware drivers, they do not need the secret calibration method.
This approach also helps you manage work better. It forces you to define scope, which makes delivery faster and cleaner.
Use clean handoff points for contractor work
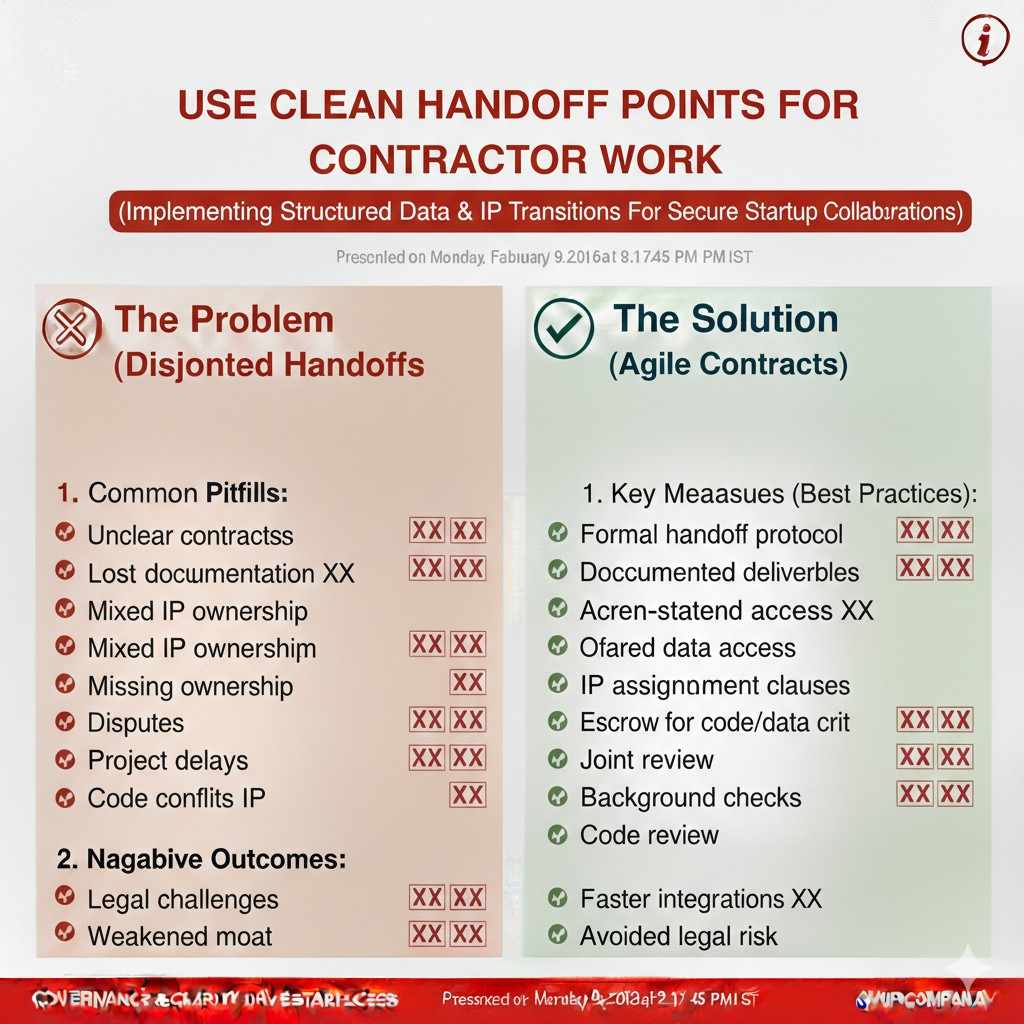
When contractors work inside your systems, secrets can leak through small things like logs, debug files, or local copies.
A clean approach is to set up handoff points where deliverables are merged and reviewed by a core team member, rather than letting a contractor freely roam.
This protects your secrets and improves code quality. It also makes it easier to remove access when the work ends.
Limit what shows up on screen shares
Screen shares are a silent leak.
People share a screen to explain a bug or show a result, and the secret is right there in a file tree, a code comment, a dataset path, or a “private” diagram.
In deep tech, even a small detail can reveal the real trick, especially to a skilled listener.
Build a “demo mode” habit
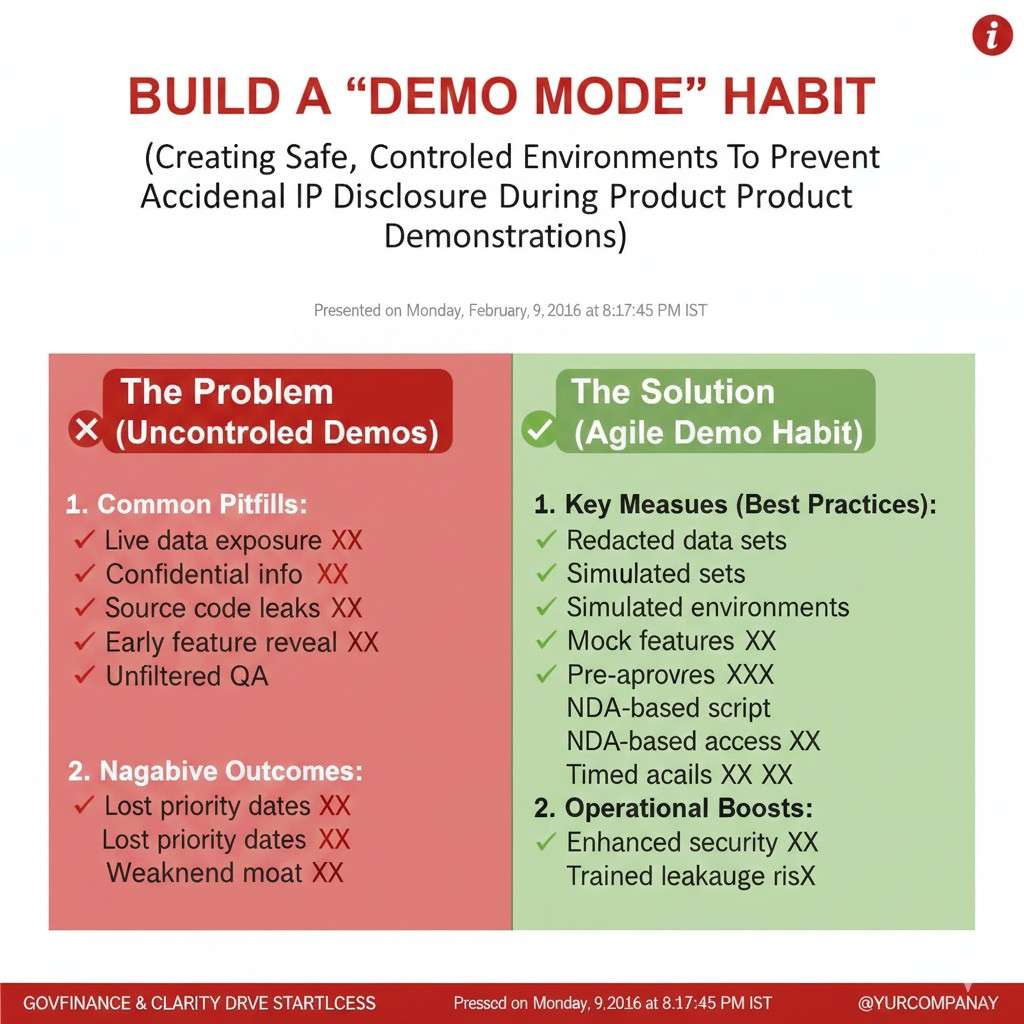
Before any investor call, partner call, or external demo, someone should switch to a clean browser profile and a clean folder view.
Use prepared slides or a prepared notebook output rather than live browsing through sensitive files.
If you must do a live demo, keep it in a controlled environment where the restricted zone is not visible by default.
Make it easy for the team to do the right thing
People break rules when the rules make work harder.
So instead of telling the team “Be careful,” you make a setup where the safe option is also the easy option.
That means having a clear place to store secrets, clear links to share, and clear rules on what goes where.
When the system is simple, people follow it without thinking.
Where Tran.vc fits in this part of the work
Many founders try to solve trade secrets with documents alone.
But real protection comes from pairing documents with real operating habits, and aligning those habits with your patent strategy.
Tran.vc helps deep tech teams decide what should be patented early, what should stay secret, and how to build clean controls that investors respect.
If you want a founder-friendly plan that does not slow down your build, you can apply anytime here: https://www.tran.vc/apply-now-form/
People Processes That Protect Secrets
Why people are the real system
Trade secrets are protected by behavior, not by hope.
Most leaks happen through normal work: a new hire onboarding, a team member switching roles, a contractor finishing a sprint, or a founder excitedly explaining the product.
So your people processes must be clear enough that they work even when you are moving fast.
Onboarding is where you set the tone
On day one, most startups talk about product and culture.
Very few talk about sensitive information in a simple, direct way. That is a mistake.
Your goal is not to scare people. Your goal is to give them confidence and clarity about what to do.
The one conversation every new hire should get
Each new hire should hear a short explanation of what your crown jewels are, where they live, and how the team shares information safely.
This is not a long training. It is a clear message that says, “We build valuable things here, and we protect them like professionals.”
When you do this early, people stop making accidental mistakes.
Written agreements matter, but they are not enough
Yes, you need strong agreements with employees and contractors.
But agreements do not stop accidental leakage. They only help after damage is done.
The day-to-day protection comes from habits: where information is stored, how it is labeled, and what is shared in casual tools.
Think of agreements as the seatbelt. Think of processes as the brakes.
Keep role changes clean and intentional
In startups, people wear many hats. That is normal.
The risk comes when access grows over time and never shrinks.
A person who moved from robotics testing to product management might keep access to restricted engineering docs just because nobody removed it.
That is how trade secrets spread inside the company without anyone noticing.
Offboarding is the moment most founders avoid
Offboarding feels awkward, especially when the person leaving helped build the early product.
But this is the moment trade secrets are most vulnerable.
People leave with laptops, personal notes, local copies, and mental models. You cannot erase what they know, but you can control what they keep in files and access.
Make offboarding a standard checklist, not a personal judgment
The best offboarding is calm and routine.
Access is removed the same day. Accounts are closed. Devices and keys are returned. Sensitive files are confirmed to be in company systems.
When you treat offboarding as normal process, nobody feels accused. It is simply how the company operates.
Exit interviews should include a quiet reminder
A short reminder during the exit process helps a lot.
It should be respectful and clear: confidential information stays with the company, and company materials must not be kept or shared.
This is not a threat. It is a professional boundary.
The founder risk: oversharing when excited
Founders are often the biggest leak risk, because founders love the work and want others to understand it.
The problem is that deep tech is easy to copy once the key trick is clear.
So founders need a safe way to tell the story without giving away the recipe.
Build “approved language” for sensitive topics
This is where the share version in your trade secret map becomes valuable.
You prepare simple, strong language you can use in investor meetings, partner talks, and recruiting.
You explain the outcome and the advantage, but you keep the exact method private.
That way you sound confident and specific, without handing over the crown jewels.
Recruiting without leaking
Hiring requires talking about the problem and your approach.
But you can recruit strong talent without showing the full secret.
Share what the work feels like, what tools you use, what challenges you face, and what success looks like.
Keep the special algorithm steps, unique data tricks, and internal methods inside the company until someone is officially onboarded and properly trained.
External Sharing Without Losing Control
Why outside talks are risky in deep tech
Deep tech teams need investors, partners, pilots, and early customers.
That means you must talk. You must show progress. You must build trust.
The danger is that every outside conversation creates a chance for your core method to slip out in small pieces.
NDAs are useful, but they do not replace process
Many founders think an NDA is the solution.
An NDA can help, but it does not stop someone from learning your approach and building a similar one later, especially if you shared too much.
The best practice is simple: share only what you need to share, even under NDA.
Treat every external meeting like a controlled demo
Before an external meeting, decide what you will show and what you will not show.
If the meeting is with a potential customer, focus on results, reliability, safety, and integration.
If the meeting is with an investor, focus on the problem, the market, why your approach works, and what makes it hard to copy.
In both cases, keep the detailed “how” inside your restricted zone.
Beware of “helpful” technical deep dives
Smart investors and partners ask deep questions.
This is normal. But deep questions can also pull secrets out of you, piece by piece.
The safe approach is to answer at the right level.
You can explain the category of method, the design choices, and the tradeoffs, without revealing the exact steps or parameters that make your system special.
The safest way to share is to share outcomes and constraints
Instead of sharing the exact training pipeline, share the outcomes it produces and the constraints it handles.
Instead of sharing the calibration math, share the stability it delivers and the conditions it survives.
This keeps the conversation real and technical, but does not expose the recipe.
Partnerships need boundaries from day one
Partnership discussions often start friendly and open.
Then someone asks for a “small sample” or “a quick look” to validate.
This is where founders accidentally hand over the core.
A safer approach is to provide a limited evaluation that proves value without exposing the key method, and to define data and IP boundaries clearly before deeper access is granted.
Customer pilots can leak through support channels
When you run pilots, you often create shared docs, shared tickets, and shared logs.
Those logs can include internal paths, model behavior notes, debug screenshots, and system details that reveal your approach.
So you want a pilot support process that filters what leaves your company.
The easiest way is to keep internal debugging in internal systems, then send only the needed outcomes and next steps to the customer.
Investor data rooms should be curated, not dumped
During fundraising, founders often create a data room and upload everything.
That is a mistake.
You do not need to share the crown jewels to raise. You need to share evidence of progress, a credible plan, and proof that your advantage is real.
A curated data room reduces risk and makes you look more disciplined.
How Tran.vc supports safe sharing and fundable IP
Tran.vc helps founders build the right blend: trade secret processes that actually work, and patent strategy where patents make sense.
This is how you raise with leverage, not desperation, because you can show investors you have a real edge and you treat it like an asset.
If you want support setting this up early, you can apply anytime here: https://www.tran.vc/apply-now-form/
