Export controls sound like a big-company problem.
They are not.
If you build robots, AI systems, chips, sensors, drones, advanced cameras, autonomy stacks, encryption, or anything that helps machines “see, decide, move, or secure,” export rules can touch you earlier than you think. Sometimes before you ship a single product. Sometimes before you even have a customer.
And here’s the part most founders miss: export controls are not only about sending boxes overseas. They can apply when you share code with a teammate in another country, let a foreign national intern access certain files, upload a model to a server outside the U.S., demo a capability to the wrong audience, or publish technical details that cross a line.
This article is a practical guide for deep tech teams. Not to scare you. To help you move faster with fewer surprises.
And if you’re building something defensible and you want to protect it early, you can apply anytime at https://www.tran.vc/apply-now-form/ — Tran.vc helps technical founders turn inventions into real IP assets, with up to $50,000 in-kind patent and IP services, so you can build leverage before your seed round.
What export controls really are (in plain words)

Export controls are rules that limit how certain tech, software, and know-how can be shared across borders or with certain people.
The goal is national security and foreign policy. Governments try to stop sensitive tech from helping military programs, surveillance abuse, or weapons work. That’s the “why.”
The “how” shows up as paperwork, restrictions, licenses, and sometimes strict “do not share” rules.
For a startup, export controls often feel like a fog because:
- The rules are written for huge defense firms, not five-person teams.
- The terms are confusing.
- Your product changes every month, so classification feels impossible.
- People think “we’re too small to matter.”
- Sales pressure makes teams ignore it until something breaks.
The fastest way to cut through the fog is to learn the few core ideas that drive almost every export control situation.
The first big idea: “Export” does not only mean shipping
In export control land, an “export” can happen when:
You send hardware abroad, sure. But also when you email controlled technical info to someone outside the U.S. Or when a team member in another country opens a controlled design file. Or when you give a product demo that reveals controlled performance details. Or when you push source code to a repo that a foreign person can access.
There is also a concept called a “deemed export.” In simple terms, if controlled tech is shared with a foreign national inside the U.S., the government may treat it like you exported it to that person’s home country. This can matter for hiring, interns, contractors, visiting researchers, and even some advisors.
This is why export controls show up early for deep tech startups. Even if you have no international sales, you probably have international people, cloud tools, and global collaboration.
The second big idea: export controls are “tech + destination + end use + end user”

Founders often ask, “Is my product controlled?”
That’s not the full question.
A better question is: “Is this specific tech controlled for this destination, for this end use, and for this end user?”
A robotics sensor might be fine to sell to one country for factory safety, and restricted to another country, or restricted if the end use is unmanned military systems, or restricted if the buyer is a blocked entity.
So it’s not only what you build. It’s also who gets it and why they want it.
The third big idea: there are different rulebooks
Most deep tech export issues in the U.S. fall under a few major buckets:
There’s a rulebook for “dual-use” items (things used for civil and military purposes). Many AI, robotics, sensors, materials, and software items land here.
There’s a rulebook for “defense articles” (true military items). If your tech fits here, the rules can be stricter.
There are also sanctions rules, which can block business with certain countries, groups, and people, even if the item itself is not special.
You do not need to memorize agencies and acronyms to act smart. But you do need to respect that multiple rule sets can apply at the same time.
A simple way to think about it:
Export controls classify the tech.
Sanctions and restricted party rules classify the counterparty and location.
Both can stop a deal.
Why this matters for deep tech

Let’s get very real about what happens when you ignore this.
Deals stall at the worst time. A strategic partner asks for export classification. You don’t have it. You scramble. Weeks pass. The partner moves on.
Your cloud setup creates a silent problem. You store controlled design files on servers outside your country by default. You didn’t mean to export. But the rules might not care about intent.
Hiring gets messy. You bring in a brilliant engineer, but your work includes controlled tech. Now you’re unsure what they can access, and your team gets awkward. This is avoidable with planning.
You can also lose trust. Investors, acquirers, and large enterprise customers do diligence. If you look like you have no export story, they worry you’re a risk.
The point is not fear. The point is readiness.
Export controls are like taxes. You do not need to love them, but you do need a system.
And the system can be lightweight if you start early.
The founder’s “export control trigger list”
You do not need to treat every startup like it’s building missiles. But there are patterns where export controls show up more.
If you do any of the following, you should assume export controls might apply and take a first pass:
You build drones, autonomous vehicles, or navigation systems.
You build robots that can operate in harsh places, do remote work, or have advanced autonomy.
You work with high-end cameras, night vision, thermal imaging, radar, lidar, or signal processing.
You build chips, chip design tools, advanced semiconductors, or hardware that boosts compute.
You build encryption, secure comms, key management, advanced cybersecurity tools, or intrusion tech.
You build AI models for targeting, surveillance, face recognition, behavior prediction, or large-scale monitoring.
You work with high-performance materials, composites, lasers, advanced batteries, propulsion, or manufacturing systems.
You work with satellites, space systems, remote sensing, or earth observation.
This does not mean “you are banned.” It means “don’t guess.” Get clarity early.
Also, remember: sometimes the “core” product is not controlled, but a module is. A tuning script. A dataset pipeline. A firmware feature. A performance spec.
The fastest practical approach: build a simple internal export control map
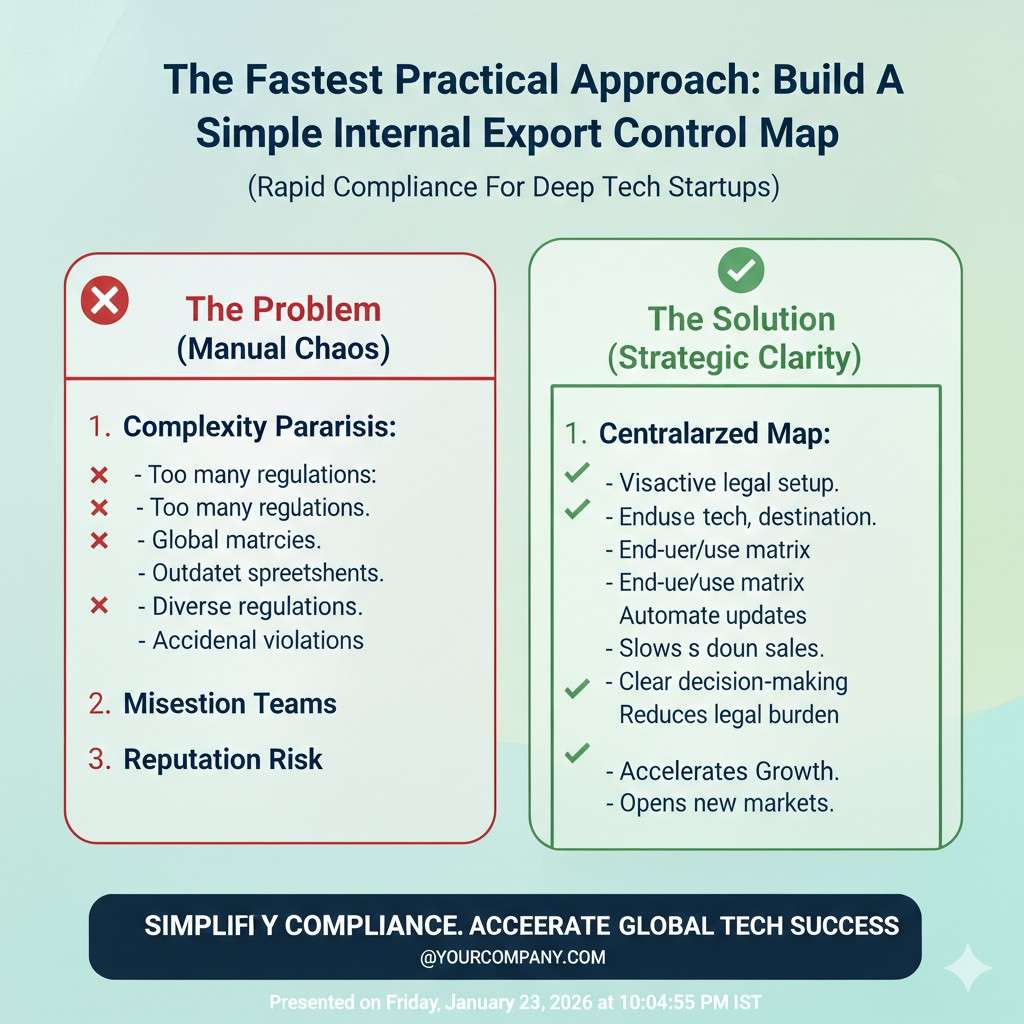
Most startups make this too heavy. They imagine a giant compliance machine. That’s not what you need.
You need a simple map that answers, in plain language:
What parts of our tech might be controlled?
Where does it live (repo, cloud, devices)?
Who can access it?
What countries do we deal with now or soon?
What types of customers are we targeting?
This is not a legal classification yet. It’s a founder-level “reality check” so you can spot risk early.
A good map can fit in a short doc that you update every quarter.
And this map pairs nicely with your IP strategy. When you document what is special and sensitive, you also get sharper on what is patentable and where your moat is.
That’s part of why Tran.vc focuses on IP-first work. Strong IP and smart controls both come from the same habit: knowing what is truly unique in your system. If you want help building that foundation, apply anytime at https://www.tran.vc/apply-now-form/
The two questions that save you from most mistakes
When someone asks for access, a demo, a repo link, or a partnership, train your team to pause and ask two questions:
What exactly are we sharing?
Who exactly is receiving it, and where are they located?
That’s it.
Most export control problems happen because teams share too much, too fast, without defining scope, or without checking who is on the other end.
If you build this into your culture early, you avoid 90% of the drama later.
Classification: the part everyone avoids
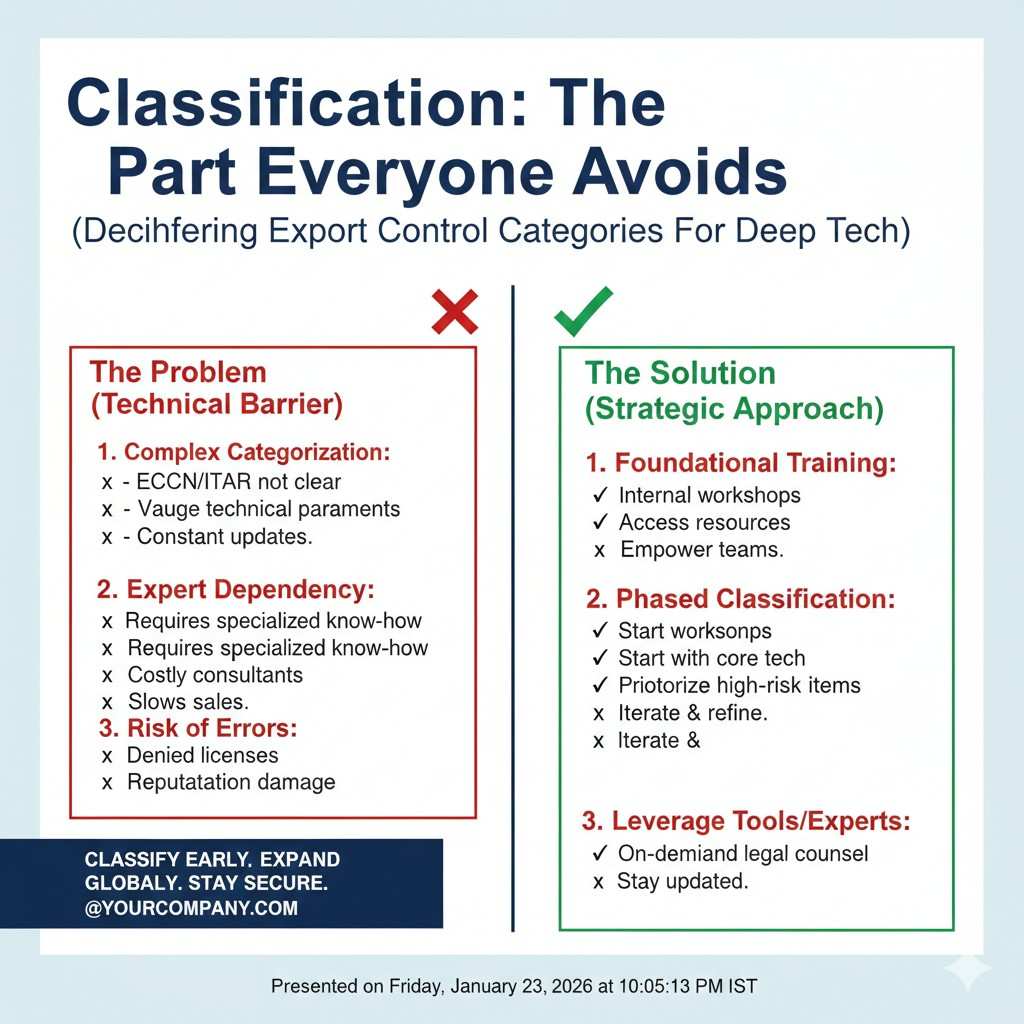
Export control “classification” is the process of placing your item, software, or technical data into the right category under the rules.
Founders hate this because it feels like decoding a secret manual.
Here’s a simpler way to think about it:
Classification is just saying what your thing is, in the language regulators use.
If you get it right, you know when you need a license and when you don’t.
If you get it wrong, you can block yourself from markets, or worse, violate rules without knowing.
Now, you do not need to do perfect classification on day one. But you do need a plan to get to “good enough” before you scale sales, partnerships, hiring, and cloud deployments.
A practical stage-based view looks like this:
Early stage: identify likely control areas and keep sensitive parts contained.
Before serious enterprise deals: get a formal classification done for key products, software, and technical data.
Before global expansion: build repeatable review steps into sales ops, contracts, and engineering release.
The easiest way to reduce export friction: separate your stack
This is a product design trick that also helps compliance.
If your system has a part that might be controlled, you want it cleanly separated from parts that are not.
That way, you can sell the “safe” core widely, and treat the sensitive module differently.
For example, you might have:
A general robotics platform that is widely usable.
A specific autonomy feature tuned for high-risk use cases.
A perception module that unlocks high-end performance.
A secure comms layer with stronger encryption features.
If you keep those separated, you can:
Limit who has access internally.
Limit what is shared in demos.
Offer different versions for different markets.
Make classification and licensing easier later.
And you also make IP strategy easier, because your invention boundaries become clearer.
This is not only legal hygiene. It is business leverage.
Export controls and AI: where teams get surprised
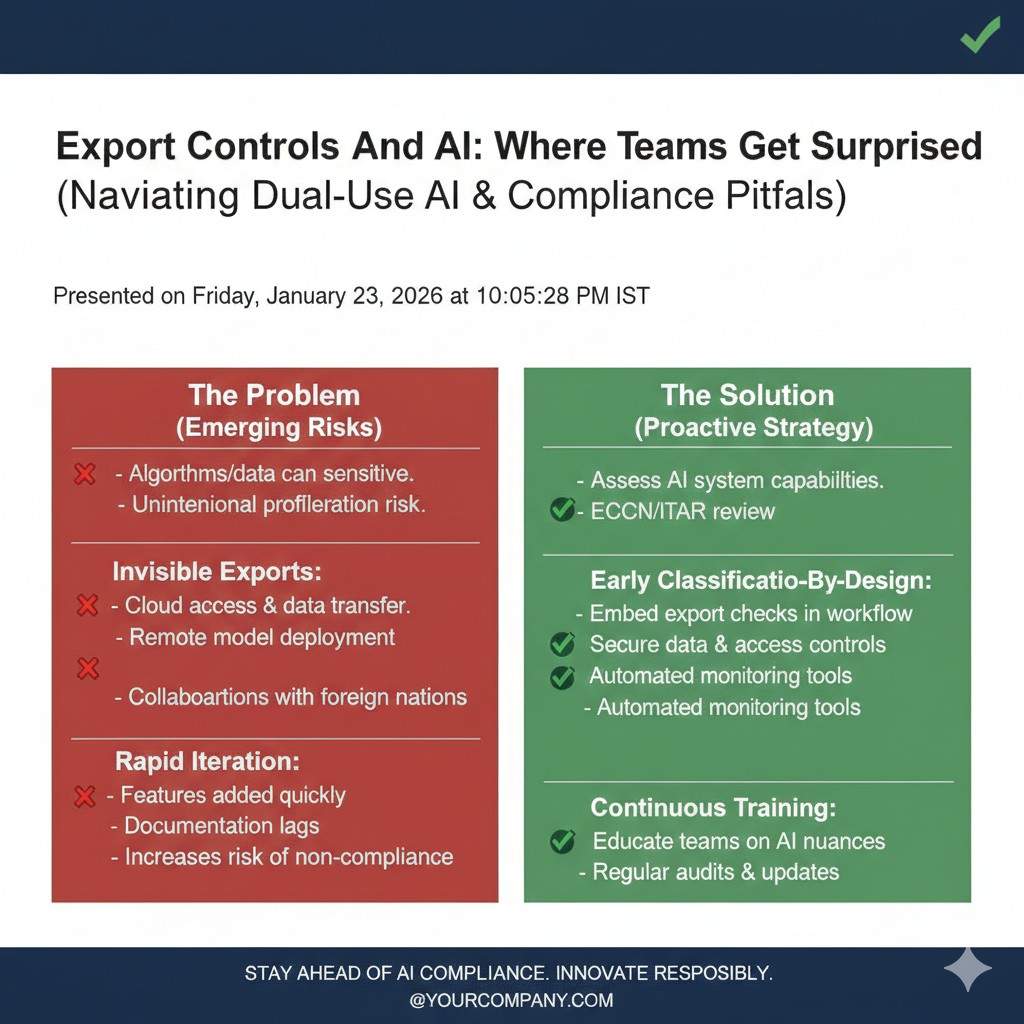
AI teams often assume export controls only apply to physical gear.
But AI touches export controls in several ways:
Model weights and training code can be treated like software.
Technical details about performance, deployment, and use can be treated like technical data.
Some use cases can trigger restrictions even if the model is general.
Also, the infrastructure matters. If controlled software is hosted on servers outside your country, you may be exporting it. If foreign nationals can access controlled parts of your system, you may have a deemed export issue.
The safest mindset is: treat your model pipeline like a product you export every time you share access.
This pushes you to do basic access control, logging, and segmentation early. Which you should want anyway.
A simple internal policy that won’t slow you down
When startups hear “policy,” they imagine bureaucracy.
But one page can cover what you need:
What files, repos, or folders are “restricted.”
Who can approve sharing restricted items.
How to do quick restricted party checks for new customers.
What to do before sending sensitive specs, source code, weights, or design files.
Where to ask questions internally when something feels off.
If you build it right, the policy becomes a speed tool. People stop guessing. They know the path.
And when you onboard new hires, you reduce accidental leaks.
Red flags in deals and partnerships

Most export control pain shows up in partnerships, not in direct sales.
Watch for these moments:
A partner asks for full source access “to evaluate.” That is often too broad. You can provide a smaller test harness or limited interface instead.
A customer wants detailed performance specs that reveal sensitive capability. You can share ranges or outcomes without revealing exact thresholds.
A foreign distributor wants to re-sell into unknown markets. That can create serious end-user risk.
A university lab wants to publish joint work with high detail. That can collide with controls and IP plans. You need a plan before you start.
A defense-adjacent buyer wants quick delivery and “off the books” language. Walk away. That is not a real customer. It is a liability.
This is where a calm, prepared founder wins. You don’t say “no.” You say, “We can support evaluation in a controlled way.”
How to build an “export-safe demo”
A demo is often an export event because it can reveal technical data.
So design your demo like you design security: assume you don’t fully control who sees it.
Practical habits include:
Avoid showing internal tuning dashboards that reveal sensitive performance.
Avoid exposing detailed sensor specs or detection ranges in slides.
Use pre-recorded video when you need to control what is visible.
Keep a “public deck” and a “restricted deck,” and treat the restricted one like you would treat a private repo.
Train your team on what not to answer live. Not because you’re hiding. Because you’re being responsible.
Hiring and “who can access what”
This is delicate, and it deserves clear thinking.
If you work with controlled tech, you might need to limit access by citizenship or immigration status for certain parts of the work, depending on the rules.
This is not about bias. It’s about legal permission.
The mistake startups make is waiting until the team is built, then discovering that access limits apply. That creates pain and can feel unfair.
The better path is:
Know early if your tech is likely controlled.
If yes, design the work so sensitive parts are isolated.
Then you can hire globally while keeping restricted work in a small ring.
This is another case where good architecture equals business speed.
Where patents fit into this
Export controls and patents sound like separate worlds, but they collide in one place: what you choose to disclose, when you disclose it, and how you control it.
If you publish too much too early, you can create export headaches and weaken your IP position.
If you keep everything secret with no IP plan, you might slow partnerships and fundraising because you cannot safely share enough.
A strong IP strategy creates a middle path:
You file early on the core invention.
You control what is shared publicly.
You structure collaborations so you can move fast without spilling the crown jewels.
That’s the Tran.vc approach in practice: build an IP-backed moat early, so you can share with investors and partners with confidence, without giving away the engine.
If you’re building deep tech and want help shaping this from day one, apply anytime at https://www.tran.vc/apply-now-form/
Export Controls for Deep Tech Startups
Why this matters sooner than you think
Export controls are not a “later” problem. They often show up while you are still building, hiring, and pitching. Deep tech moves across borders in quiet ways, like code access, cloud storage, and shared research notes.
If you wait until a big customer asks for export paperwork, you end up reacting under pressure. That is when teams make mistakes, over-share, or freeze deals because they do not know what is safe.
Tran.vc works with technical founders who want to build with leverage from day one. If you want help turning your work into protected IP while staying clean on what you share, you can apply anytime at https://www.tran.vc/apply-now-form/
What “export” really means in daily startup life
Most founders think export means shipping hardware overseas. That is only one case. An export can also be an email with technical details, a GitHub invite, a shared drive link, or a demo that reveals sensitive performance.
Even letting a person in another country view controlled design files can count. The rules care about access, not only boxes moving through customs.
The four questions that drive almost every decision
When you strip export controls down to basics, it often comes back to four questions. What are you sharing, who receives it, where are they, and what will they do with it.
If your team learns to pause and run these questions before sharing sensitive items, you avoid most surprises. It also makes your company look mature when partners and investors start asking tougher diligence questions.
How export controls are structured
The idea of “controlled items” in simple words
Export controls focus on specific items, software, and technical data that governments see as sensitive. Sensitivity is usually tied to military use, surveillance use, or the ability to strengthen another country’s strategic capabilities.
Many deep tech products are “dual-use,” meaning they can help both civil work and military work. A sensor can help a robot navigate a warehouse, and the same sensor can help a drone navigate a conflict zone.
That dual-use reality is why startups building autonomy, perception, navigation, or security tools need to pay attention early.
Classification: the label that unlocks the rules
Classification is the act of putting your product or software into the right category under the rulebook. Once you know the category, you can tell whether you need a license for a certain country or customer.
Founders avoid this because it feels like learning a new language. But you do not need to master the whole system. You need a way to get to a reasonable answer for your core product and the key technical pieces.
A common mistake is guessing, then building plans around that guess. A better approach is to create a short, living document that tracks what you believe is controlled, why you believe it, and what you still need to confirm.
Countries, customers, and end uses matter as much as the tech
Export controls are not only about what you build. They are also about where it goes, who gets it, and what they intend to do with it.
A product may be okay for one market and restricted for another. The same item can also become restricted when the end use shifts into military or surveillance work.
That is why export control is not one-time work. It is a habit built into sales, partnerships, and product releases.
The earliest risk: “deemed exports” and team access
Why hiring and interns can trigger export rules
A deemed export is when certain controlled tech is shared with a foreign national inside the U.S., and the law treats it like an export to that person’s home country. This can matter for hiring, internships, visiting researchers, and contractors.
Deep tech teams are often global by nature. That is a strength, and you can keep it. The key is to design your workflow so you are not accidentally giving full access to the most sensitive parts of the system.
When companies plan for this early, the solution is rarely dramatic. It is usually about access control, repo structure, and making sure only a small group touches the restricted layer.
How to reduce risk without harming your culture
If you handle this topic poorly, you can damage trust inside your team. People can feel singled out or blocked from meaningful work.
The way to avoid that is to frame it as architecture and process, not personal judgment. You separate sensitive modules because it helps product focus, security, and compliance.
Then you can give everyone strong work streams while limiting only the parts that truly require extra care. This becomes easier if you document your system boundaries clearly and maintain clean internal controls.
