Your idea can be brilliant. Your code can be sharp. Your robot can work on the bench.
But one loose contract can quietly hand your edge to someone else.
IP leaks rarely look like a “leak.” Most times, they look like normal startup life:
A friendly advisor asks for “a quick look” at your deck.
A contractor builds a prototype module.
A pilot customer wants early access.
A big company suggests a “partnership” and sends over their paperwork.
A new hire starts next week and wants to “review everything” today.
None of this feels risky in the moment. That is why it works.
This article is about stopping IP leaks before they happen, using contracts and NDAs in a way that is simple, practical, and founder-friendly. Not scary. Not full of legal words. Just clear moves you can use right now.
If you want Tran.vc to help you build an IP plan and protect what matters—before you raise your seed—apply here anytime: https://www.tran.vc/apply-now-form/
When people say “IP,” they often jump straight to patents. Patents matter. But the first battle is usually not in court. It is in documents. It is in who owns what. It is in what your team is allowed to share. It is in what your vendor can reuse. It is in what a customer can copy after the pilot.
Contracts and NDAs are not just “paperwork.” They are your first security system.
The real reason IP leaks happen
Most founders think an IP leak is theft. Like someone breaks in and steals files.
In early-stage startups, leaks are more often caused by:
- unclear ownership
- loose “work for hire” language
- missing invention assignment
- NDAs that do not match the real relationship
- “friendly” sharing without limits
- people leaving without a clean exit
In other words: not evil. Just messy.
Messy is dangerous because it creates a story later that sounds believable, like:
“We thought we were allowed to use that.”
“We built it, so we assumed we owned it.”
“You never told us it was confidential.”
“The NDA expired.”
“The contract says we can reuse general ideas.”
And when you are a small company talking to a big company, the “story” matters.
So the goal is not to win arguments later. The goal is to prevent the argument.
Start with a simple map: what are you protecting?
Before you touch an NDA, get clear on what you are actually trying to protect. Not in a long document. Just in your head, and maybe a short internal note.
For most AI, robotics, and deep tech teams, the crown jewels are usually one or more of these:
Your training data pipeline and labeling logic.
Your model architecture choices and tuning tricks.
Your control system logic and safety logic.
Your sensor fusion approach.
Your hardware design files and BOM details.
Your test rigs and test methods.
Your roadmap and go-to-market plan.
Your customer list and pricing.
Your source code.
Your patentable ideas that are not filed yet.
Here is the key point: some of this is patentable, some is trade secret, and some is just business-sensitive. Contracts and NDAs should cover all three, but in different ways.
If you only treat everything as “confidential,” you will either over-share or block your own speed. The best approach is to share in layers.
Avoiding IP Leaks Through Contracts and NDAs
Why this topic matters more than most founders think
Your product can be great and your team can be strong. Still, one loose document can give away the thing that makes you special. Most IP leaks do not look like theft.
They look like normal startup life. A friendly advisor asks for a quick look. A contractor helps with a module. A pilot customer wants early access. A big company sends “their standard form” and says it is simple.
That is why contracts and NDAs matter. They are not just paperwork. They are your first safety system for your ideas, your code, and your edge.
A quick note on how Tran.vc helps
At Tran.vc, we help technical founders protect what matters early. We invest up to $50,000 in in-kind IP and patent services so you can build a real moat, even before you raise your seed round.
If you want help building a smart IP plan and tightening your contracts, you can apply anytime here: https://www.tran.vc/apply-now-form/
How IP leaks actually happen in early-stage startups
Leaks usually come from “normal” sharing, not bad actors
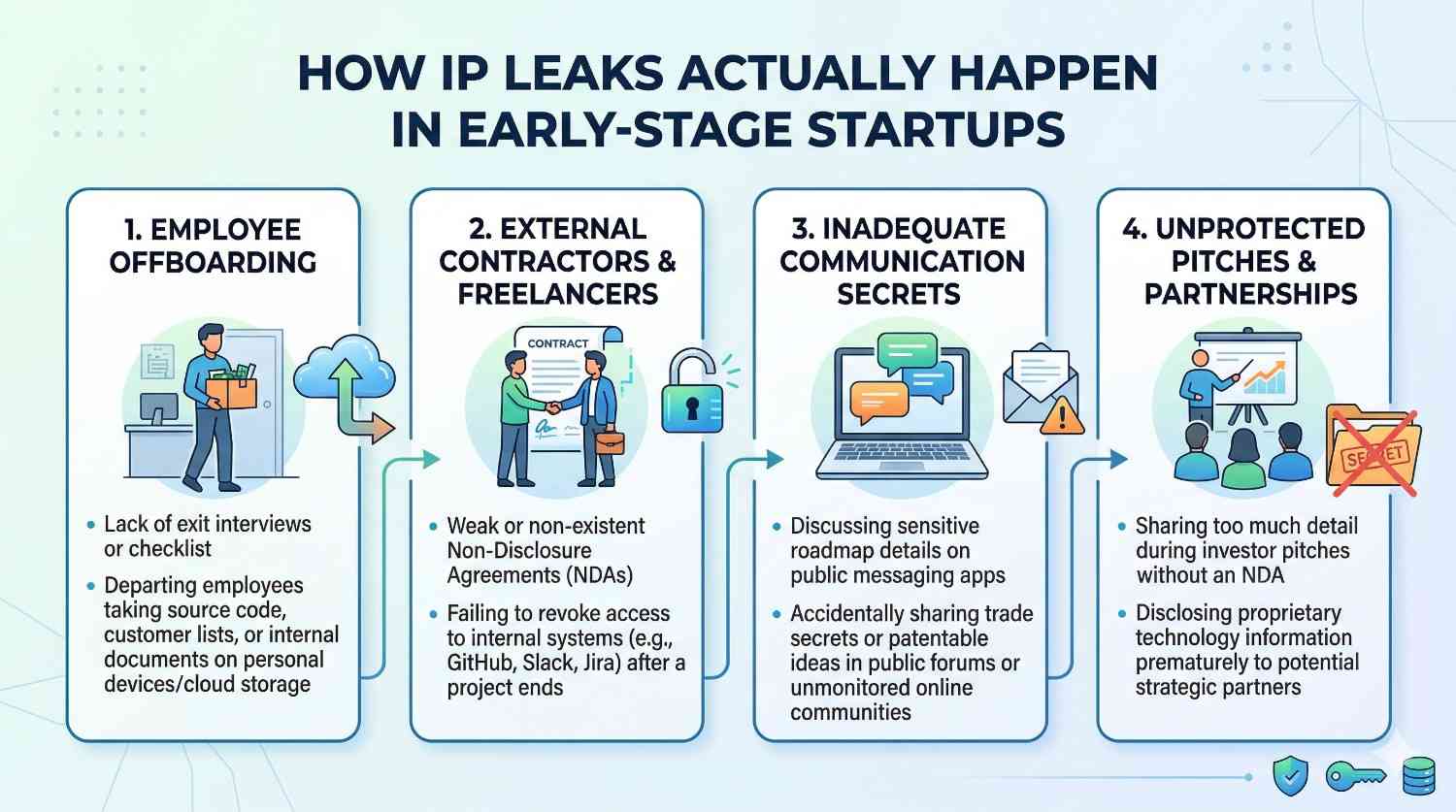
Most founders imagine an IP leak as someone stealing files. In real startups, leaks often come from simple habits: sharing too much, too soon, with unclear rules.
When people are moving fast, they forward a deck. They add someone to a folder. They explain the key idea on a call. Nobody feels like they are doing something risky.
Later, when things get serious, the story changes. People start saying, “We thought we could use that,” or “You never told us it was confidential.” If your paperwork is weak, that story can become a problem.
The biggest root cause is unclear ownership
Ownership is the center of most IP fights. If it is not clear who owns the work, then everyone has an argument later.
This happens when a founder used code from an old job. Or a contractor built something and the contract does not assign rights. Or an advisor gave “ideas” and thinks they should own part of the invention.
The fix is not to distrust people. The fix is to make ownership clear from day one, and keep it clean as the team grows.
Why deep tech teams face higher risk
AI and robotics teams often have more moving parts than a normal software startup. You may have models, data pipelines, firmware, control systems, mechanical designs, and test methods.
Each part can leak in different ways. A hardware vendor can reuse your fixture design. A data contractor can carry your labeling rules to another client. A partner can learn how you solved a hard edge case.
Because the work is complex, you need simple rules that still cover the full system.
What you are really protecting when you say “IP”
Patents, trade secrets, and business-sensitive info are not the same
Many founders call everything “confidential.” That can create confusion because not all sensitive information is the same.
Some parts of your work may be patentable, meaning you want to file on them and claim them as your invention. Other parts should stay as trade secrets, meaning you protect them by keeping them hidden and controlled.
Then there is business-sensitive information, like pricing, customer lists, and roadmap plans. These are not always “inventions,” but they still can hurt you if they spread.
A good contract approach treats these categories with care, even if the language stays simple.
Your “crown jewels” should be clear inside your team
You do not need a huge internal document. But you do need shared clarity.
Your team should know what must never be shared outside, what can be shared only under NDA, and what can be shared openly. If your team does not know the boundaries, they will guess.
Guessing causes leaks. Clear internal rules prevent them.
Protecting IP is also about timing
Timing matters because early sharing can ruin your leverage. If a partner learns the key idea before you have filing plans, you may lose control of the story.
Even if nobody steals, early sharing can reduce your negotiating power later. You want to share enough to move deals forward, but not so much that you hand away the map.
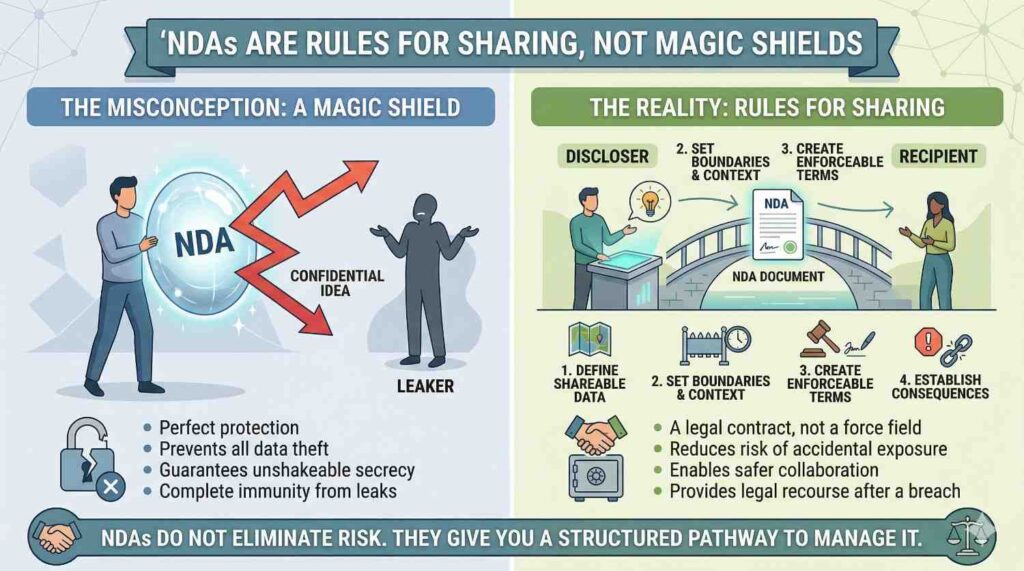
NDAs are rules for sharing, not magic shields
What an NDA does in plain language
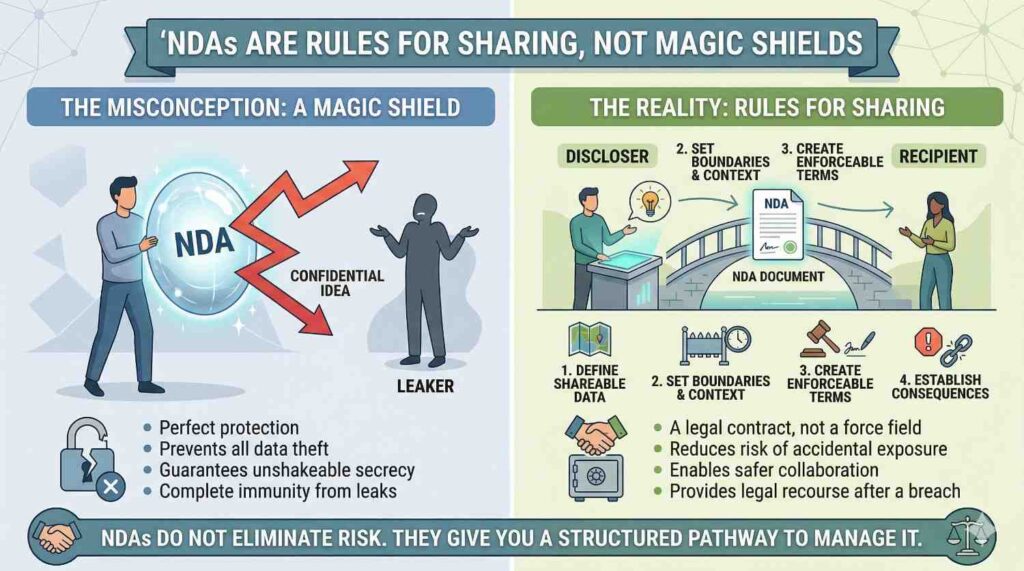
An NDA is a set of promises about information. It says what can be shared, how it can be used, who can see it, and how long the duty lasts.
It also sets expectations. If the other side knows you take confidentiality seriously, they behave differently.
But an NDA cannot fix careless sharing. If you ignore the rules in the NDA, your protection can get weaker in the exact moment you need it.
The most important NDA habit: share only what is needed
Founders often overshare because they want to look strong. They want to prove the tech is real.
The smarter move is to share in layers. Start with the problem, the approach, and the results. Keep the “how” for later, and only share the minimum detail needed to reach the next step.
This way you can move fast without giving away the core recipe.
The marking and process details matter more than people think
Some NDAs require you to mark documents as confidential. Some require written follow-up if you share confidential info on a call.
If you ignore those steps, the other side can later argue that the info was not covered. It sounds unfair, but it is common.
A simple internal practice helps: label the files, keep a short record of what you shared, and follow up after sensitive calls with a brief note that the details are confidential under the NDA.
Choosing the right NDA for the situation
One-way vs mutual: pick what matches reality
A one-way NDA is best when you are the main party sharing sensitive information. This is common when you are pitching a customer, a partner, or a large company that wants to evaluate your product.
A mutual NDA makes sense when both sides will share meaningful secrets. This can happen in co-development, joint research, or deep partnership work.
If you accept a mutual NDA just because it is “standard,” you might end up with language that does not protect your side well. The right choice depends on who is actually exposing risk.
Short-term discussions vs long build partnerships
The NDA you use for a quick evaluation should not look like the one you use for a long co-build.
For short talks, keep the scope tight and the rules clear. For long partnerships, you may need extra terms that control how teams interact, what gets created, and how ownership works.
If you use a thin NDA for a deep partnership, you are often missing the most important part: how new work is handled.
Investors and NDAs: a practical reality
Many investors will not sign NDAs. This is common, not personal.
The right move is to adjust what you share. You can talk about outcomes, traction, and high-level methods without handing over the secret sauce.
If you need Tran.vc’s help shaping what to share and how to protect your core, you can apply anytime here: https://www.tran.vc/apply-now-form/
Common NDA traps that cause leaks later
The term is too short for deep tech timelines
Many NDAs set confidentiality for one or two years. That can be fine for some markets. For AI and robotics, it is often too short.
If your product cycle is long, your competitive risk lasts longer. If the NDA ends before you launch, the other side may later claim they are free to use what they learned.
A better approach is a longer period for confidential info, and special treatment for trade secrets that stays in place as long as the information stays secret.
“Residuals” clauses that quietly weaken your protection
A residuals clause may say that a person can use information that remains in their memory, as long as they do not copy documents.
That sounds harmless, but it creates a big hole. People can “learn” your approach and later build something similar while claiming it is based on general knowledge.
If you see residuals language, treat it as a major risk. Many startups choose to remove it or narrow it heavily, especially when core technical methods are being shared.
Broad “purpose” language that lets the other side use your info widely
An NDA should limit use to a clear purpose, like evaluating a partnership or running a pilot.
If the purpose is written too broadly, the other side can argue they were allowed to use your confidential info for many internal projects. This is common when the other side’s legal team uses a one-size form.
A tight purpose clause is one of the simplest ways to reduce leak risk without adding complexity.
Weak control over “who can see it”
An NDA often allows sharing with employees, agents, or contractors who “need to know.” That is normal.
The problem is when “need to know” becomes “anyone.” If your sensitive details spread across a large team, it becomes hard to track and harder to contain.
A good NDA limits access, requires those people to be bound by similar duties, and sometimes asks the receiving party to take reasonable security steps.
Contracts do more than NDAs: they decide who owns what
NDAs protect sharing, but contracts protect creation
An NDA is mostly about information you already have. A contract is often about work that will be done in the future.
If a contractor builds a module, or a partner co-develops a feature, you must define ownership of the output. Otherwise, you might pay for work and still not fully own it.
This is the most common place founders lose control without noticing. It is not dramatic. It is just missing language.
Work-for-hire is not enough by itself
Many founders think “work for hire” solves ownership. In practice, it is not always enough, and it can be limited depending on the type of work and local rules.
The safer pattern is clear assignment language. The contract should say that all rights in the work product are assigned to your company, and that the contractor will sign further papers if needed.
It should also cover inventions, not just code. In robotics and AI, inventions can exist in test methods, data workflows, and system design choices.
The contractor’s “background IP” must be handled carefully
Contractors and vendors often bring their own tools and libraries. That is normal.
But you need to make sure their background IP does not become a chain around your ankle. If your product depends on something they own, you might be stuck.
A good contract makes a clear line between what they already had before the work and what they create for you during the engagement. It also makes sure you get the rights you need to use and ship the deliverables.
The “reuse” clause can become an IP leak
Some vendor contracts include language that allows them to reuse “general ideas” or “non-confidential know-how” from the project.
If your work is specialized, that reuse can effectively mean they can build a similar solution for another client. That is a quiet leak.
If you are paying for custom work that touches your core advantage, push to limit reuse. At minimum, block reuse of your specific designs, your data, and your system-level methods.
Managing IP risk with advisors, mentors, and consultants
Why informal roles create formal risk

Advisors and mentors often start as friendly helpers. They give feedback over coffee, review a deck, or make a few introductions. Because the relationship feels informal, founders often skip formal paperwork.
This is exactly where IP risk hides. When someone contributes ideas, frameworks, or technical suggestions, they may later believe they have rights. Even if they never intended harm, memory and incentives can change.
A simple advisor agreement and NDA sets expectations early and keeps the relationship clean as the company grows.
Advisor agreements should be simple but clear
An advisor agreement does not need to be long. It needs to answer a few clear questions in plain words.
It should say that the advisor’s role is advisory, not operational. It should say that any ideas or suggestions they provide belong to the company. It should also say that they will keep company information confidential.
This protects both sides. The advisor knows where they stand, and you avoid confusion later when investors start asking hard questions.
When consultants cross into invention territory
Consultants often start with narrow tasks, like reviewing data quality or tuning a model. Over time, their input can shape core technical decisions.
If the contract does not assign inventions, the consultant may legally own part of what they helped create. This can show up during diligence and slow everything down.
Before the work starts, make sure the contract clearly assigns all inventions and work product to your company, even if the consultant only worked a few hours.
Employee contracts are your first real IP firewall
Every founder and early hire needs clean paperwork
It is common for early teams to delay formal contracts because trust feels high. Unfortunately, trust does not replace clarity.
Every founder and employee should sign an invention assignment and confidentiality agreement. This should happen as soon as they start contributing, not months later.
If someone leaves and the paperwork is missing, fixing it later can be awkward or impossible.
Invention assignment is not just about code
In AI and robotics startups, inventions can exist outside of code. They can live in data strategies, test setups, hardware layouts, or control logic.
Your agreements should cover all inventions related to the business, not just software. This ensures that ideas created during work hours, or using company resources, belong to the company.
Clear language here makes future patent filings much smoother.
Handling prior work and side projects honestly
Employees often bring experience from past jobs or personal projects. This is normal and valuable.
The risk appears when prior work mixes with company work. If an employee reuses old code or methods, ownership can become unclear.
A good agreement asks employees to list prior inventions and clarifies that anything not listed is assumed to belong to the company if created during employment. This protects both sides by setting the record early.
Customer contracts and pilots can leak more than you expect
Pilots are where curiosity turns into copying

Pilot programs are exciting. A customer gets hands-on access, and you get real-world feedback.
But pilots also expose your system in ways a sales deck never does. Customers can see behavior, performance, and sometimes internal logic.
If the contract does not limit use, the customer may later build something similar internally or share insights with a vendor. That is not always malicious. It is often seen as learning.
Limiting use to evaluation is critical
A strong pilot agreement clearly limits how the customer can use your product and information. The purpose should be evaluation only, not internal development or benchmarking for future builds.
The agreement should also restrict reverse engineering and sharing with third parties. Without these limits, you may have little control over what the customer learns and applies later.
Data ownership during pilots must be explicit
Pilots often involve data flowing both ways. Your system may generate insights, models, or outputs based on customer data.
The contract should clearly state who owns what. You want to retain rights to your models, improvements, and learnings, even if they are trained on customer data.
This clarity becomes very important when you scale across multiple customers.
Partnerships and joint development need extra care
Joint work creates shared risk by default
When two companies build together, IP risk increases. Ideas flow both ways, teams interact, and boundaries blur.
If ownership rules are not set early, both sides may later claim rights to the same invention. This can freeze progress and scare investors.
The goal is not to avoid partnerships, but to structure them with clear lines.
Define ownership of new work before work starts
A good joint development agreement answers ownership questions up front. It says who owns improvements, who owns joint inventions, and who can use the results.
This may feel uncomfortable to discuss early, but it is much harder to fix later. Clear rules allow teams to collaborate without fear.
Control how information flows between teams
Partnerships often involve many people. If sensitive details spread too widely, control is lost.
Agreements should limit access to specific teams and require confidentiality from everyone involved. Practical controls, like shared folders with limited access, support the contract in real life.
What happens when someone leaves the company
Exits are a common source of quiet leaks
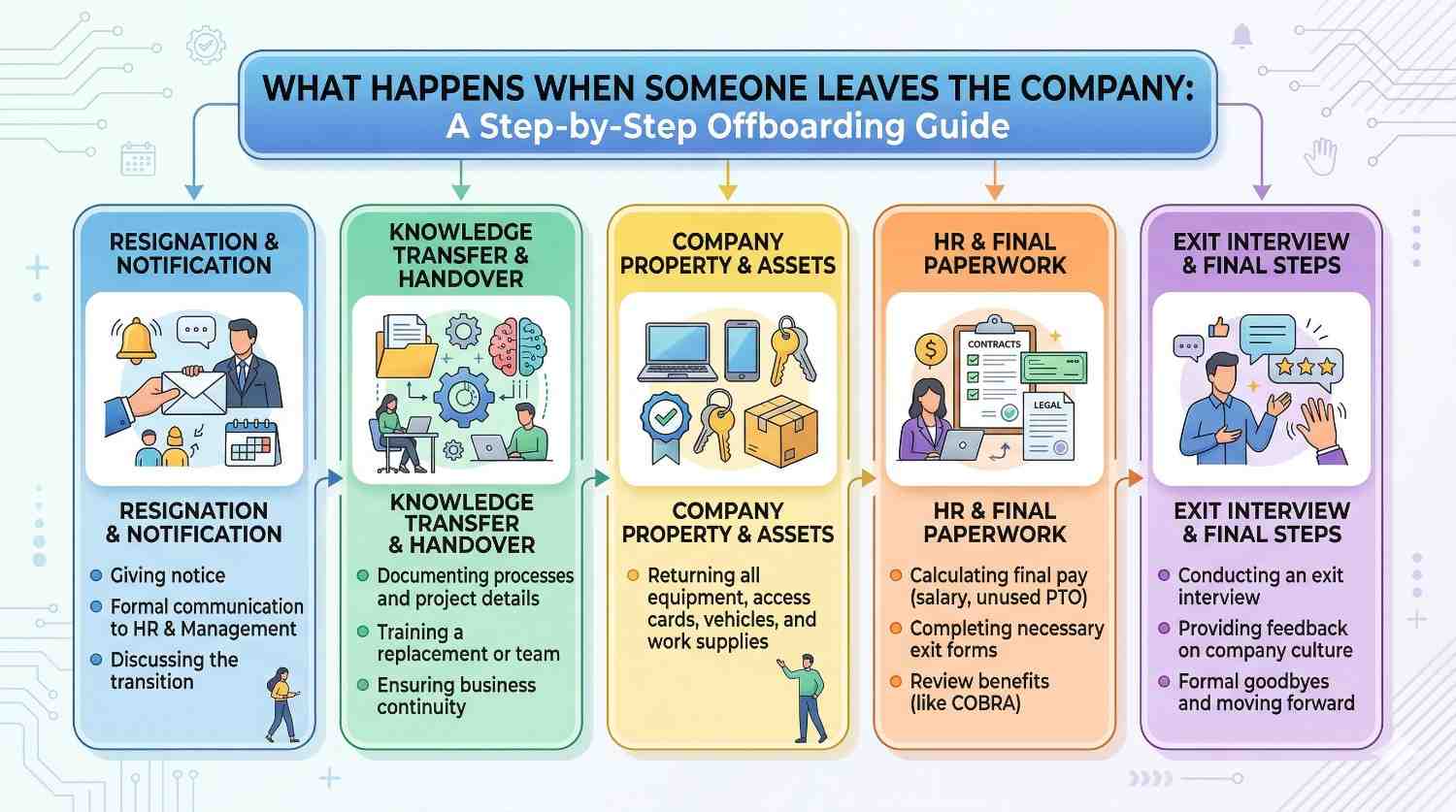
When an employee or contractor leaves, they take knowledge with them. That cannot be stopped. But misuse can be limited.
A clean exit process reminds them of their confidentiality duties, confirms return of materials, and closes access to systems.
Skipping this step creates uncertainty and weakens your position if issues arise later.
Post-termination obligations must be clear
Confidentiality should not end when employment ends. Your agreements should state that confidentiality obligations survive termination.
This does not stop someone from working elsewhere. It simply stops them from using or sharing your secrets.
Clear language here makes enforcement more realistic and less emotional.
Non-competes vs confidentiality: know the difference
In many regions, non-competes are limited or not enforceable. Confidentiality agreements are different.
You should not rely on non-competes to protect IP. Instead, focus on strong confidentiality and invention assignment. These are more widely accepted and easier to enforce.
Preparing for diligence: contracts as proof of discipline
Investors look for clean IP, not just good tech
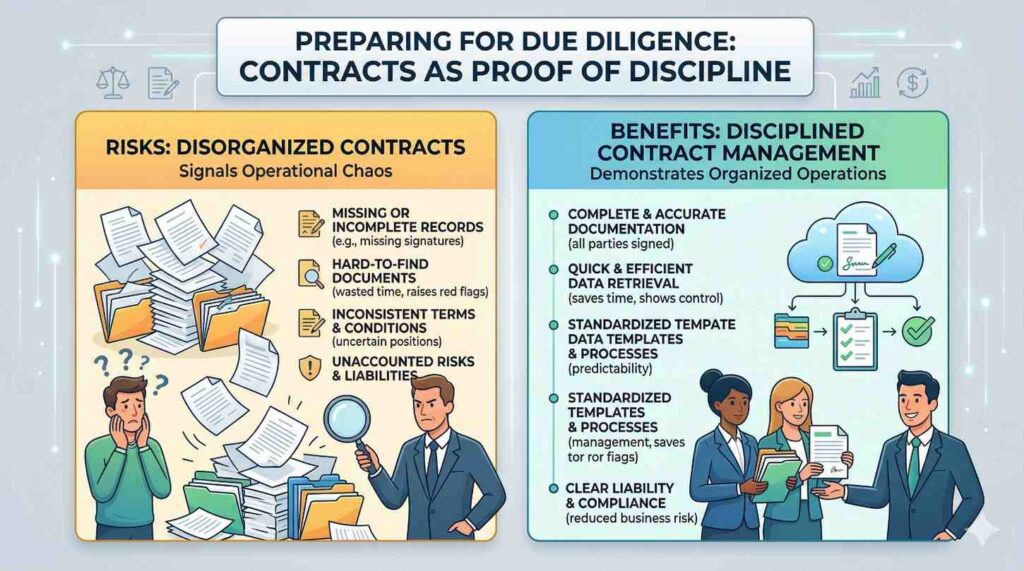
When investors review your company, they look at your contracts. They want to see that IP ownership is clear and risk is managed.
Missing agreements, unclear assignments, or messy NDAs raise questions. Even if the tech is strong, deals can slow down or change terms.
Good contracts signal that you build with intention.
Strong paperwork increases leverage, not friction
Founders sometimes fear that legal discipline slows them down. In reality, it often speeds things up.
When your IP story is clean, investors feel safer. Partners negotiate faster. Customers trust you with deeper access.
This is leverage, not bureaucracy.
How Tran.vc supports founders here
Tran.vc helps founders set up IP and contracts early, before problems appear. We invest up to $50,000 in in-kind IP and patent services so you can build a defensible foundation without burning cash.
If you want help tightening your IP posture and preparing for future diligence, you can apply anytime at https://www.tran.vc/apply-now-form/
\
