Most founders think VC due diligence is about revenue, growth, and product. It is. But for technical startups, there is another quiet deal-breaker that shows up fast once lawyers and security teams get involved: open source compliance.
If your code uses open source (and it almost always does), investors will want to know one thing: can this company own and protect what it is building, without hidden legal risk?
This matters even more for AI, robotics, and deep tech—exactly the kind of companies Tran.vc supports. When your value is in your models, training pipelines, embedded software, control systems, or edge deployments, a single license mistake can create a messy problem at the worst time: right before a priced round, a large customer contract, or an acquisition.
So this guide is about being ready before you get put on the spot.
Not with big theory. With clear, practical steps you can take now, even if you are just a few engineers moving fast.
In the next section, we’ll cover what VCs actually check, what scares them, what “clean” looks like, and how to build an open source process that does not slow your team down.
Also, if you’re building AI, robotics, or deep tech and you want to turn your tech into protectable assets early—patents, strategy, and strong IP foundations—Tran.vc can help. You can apply anytime here: https://www.tran.vc/apply-now-form/
Why VCs Care So Much About Open Source
It is not about “using open source”
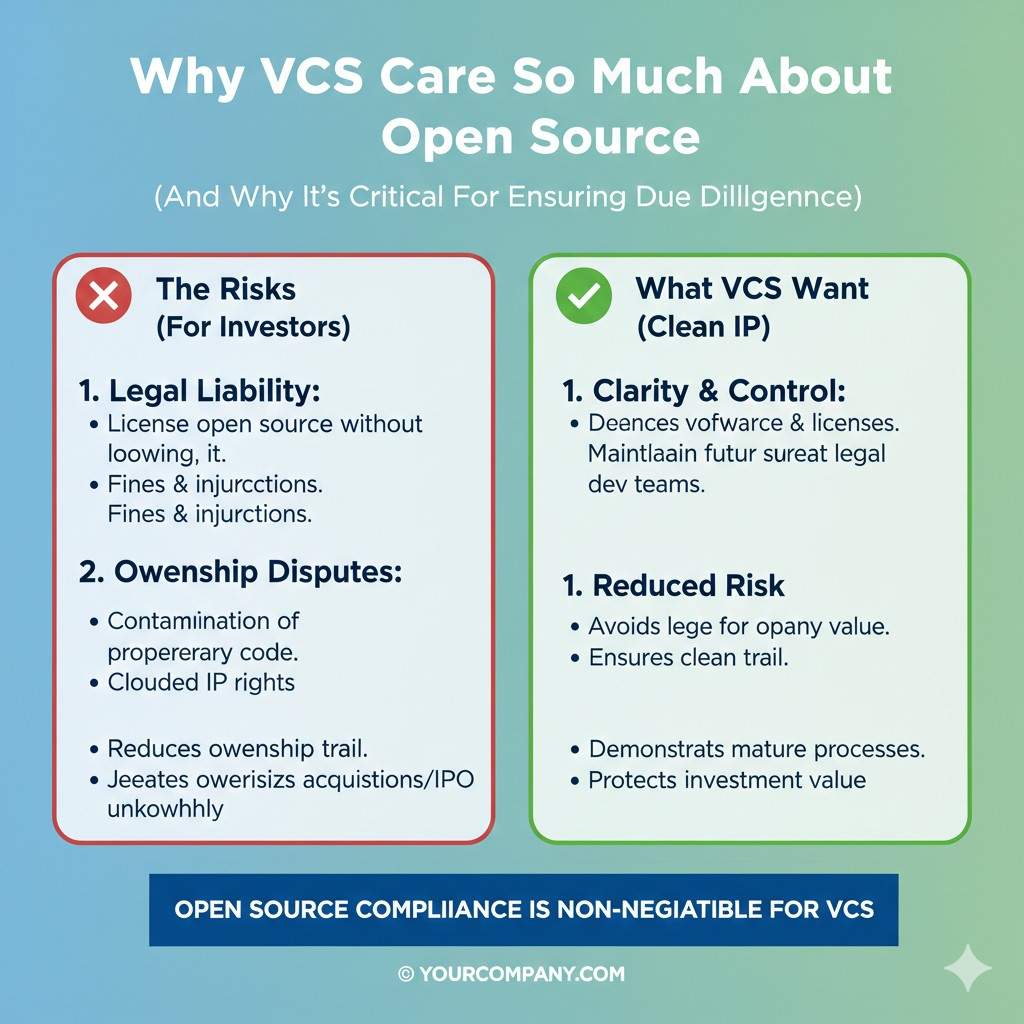
Most investors do not dislike open source. In fact, they expect it. Open source is how modern software gets built fast. The real worry is whether your company used open source in a way that quietly changes who owns the product, or what you are allowed to sell.
When a VC asks about open source, they are not trying to slow you down. They are trying to remove “unknown risk.” If they cannot measure the risk, they assume the worst. That assumption can shrink your valuation, delay the round, or cause the deal to fall apart.
Investors fear surprises more than problems
Here is what founders miss: you can often fix open source issues. What is hard to fix is trust once a problem appears late. If a VC finds out during legal review that your core product is mixed with the wrong license, they wonder what else is messy.
A clean open source story signals something bigger. It signals that the team can build serious systems, handle details, and operate like a company that will survive at scale.
Open source is tied to IP, not just legal
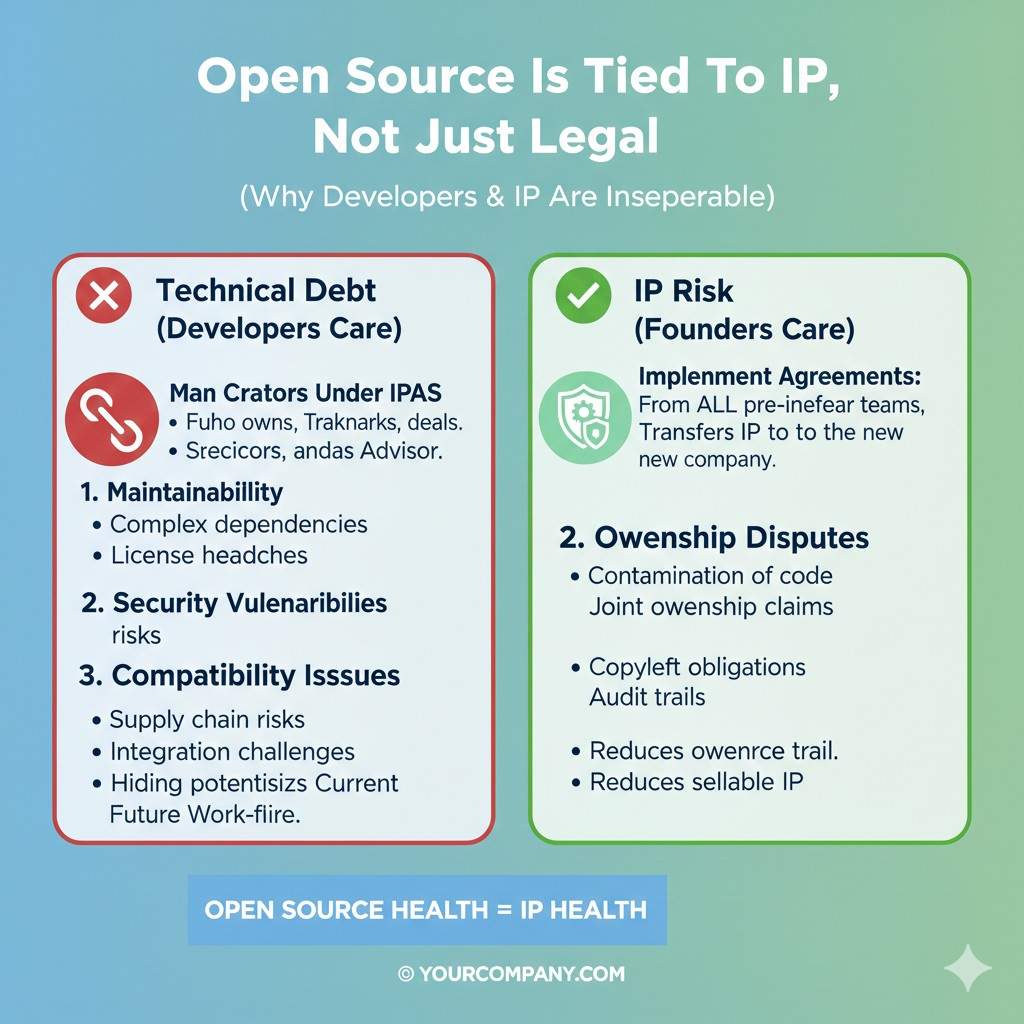
For deep tech startups, your IP story is your leverage. If you are building robotics controls, AI inference engines, data pipelines, or embedded systems, your edge is often in specific code choices and design decisions.
When open source is tangled into that edge without a clear boundary, your IP position gets weaker. That is why open source compliance is not just a “legal task.” It is part of your moat.
If you want to build that moat early, Tran.vc helps founders lock down IP strategy and patent work from day one. You can apply anytime here: https://www.tran.vc/apply-now-form/
What “Open Source Compliance” Really Means in Due Diligence
It means you can explain what you shipped
Compliance is not a fancy policy document. At diligence time, it means you can answer basic questions with confidence. What open source components are in the product, where did they come from, and what licenses do they use?
If you cannot answer those questions quickly, the investor imagines a large hidden mess. They also worry your future enterprise customers will ask the same questions and you will not have a good reply.
It means you followed the license rules

Each license comes with conditions. Some ask you to include notices. Some ask you to share changes. Some restrict how you can link code. Some require you to provide the license text with distributions.
In diligence, nobody expects perfection on day one. But they do expect you to take the rules seriously and show that you have a working process to follow them.
It means you can prove ownership boundaries
VCs want to know what the company owns and what it does not. If open source code is mixed deeply into your proprietary modules, it becomes hard to draw a clean line.
A good compliance setup keeps clear boundaries. It makes it obvious what is yours, what is third-party, and what you must do to keep using it safely.
How VCs Actually Check Open Source During Diligence
They ask for a software bill of materials
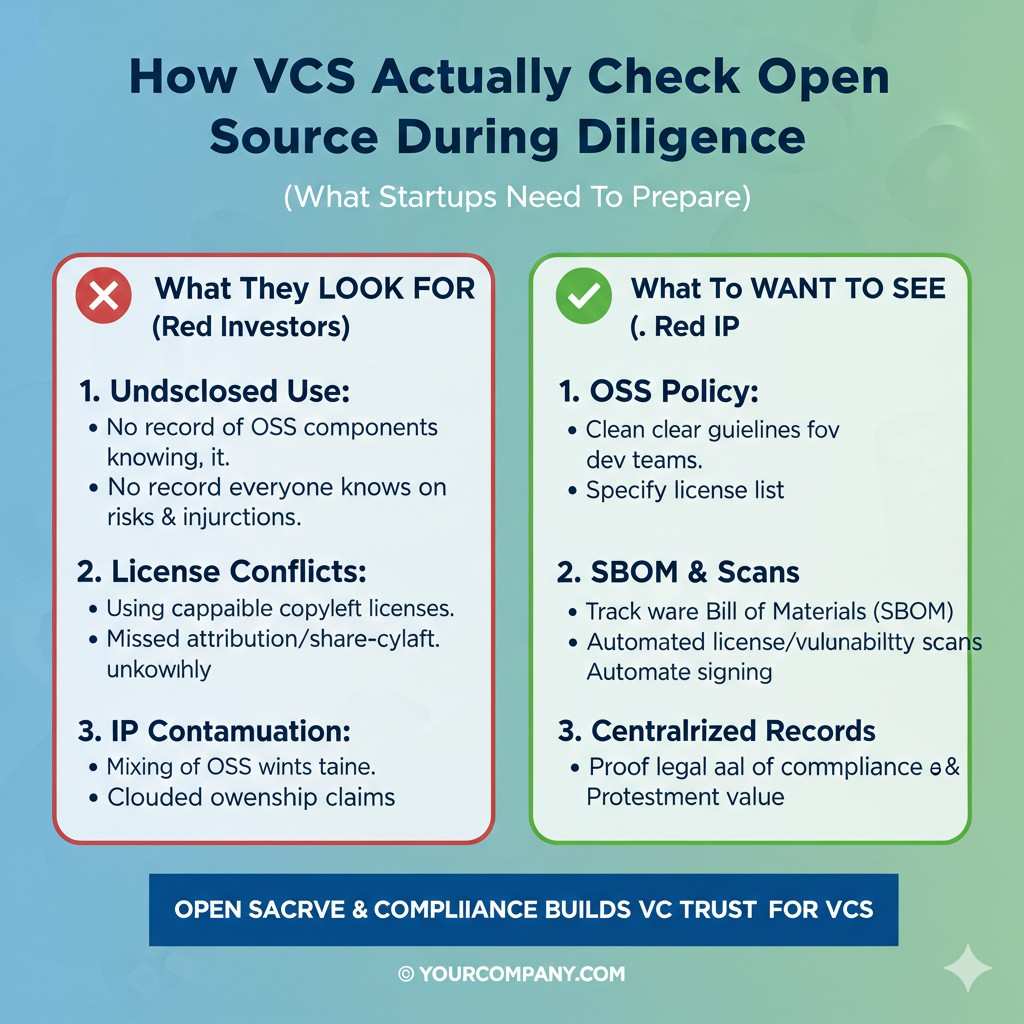
A software bill of materials, often called an SBOM, is a list of the components in your software. Some startups already have one because customers asked. Many do not.
Even if a VC does not use the word “SBOM,” they usually want the same outcome. They want a clear inventory of dependencies, versions, and licenses. They want to know you can generate it again later, not just once.
They look for high-risk license exposure
The diligence team often searches for licenses that can create obligations you did not plan for. This is where fear comes from, because founders sometimes copy code quickly and do not check what they pulled.
The review is usually not about your entire codebase. It is about your core product path. If the most valuable part of your system is exposed to the wrong license, that is what they focus on.
They check if your team has basic controls
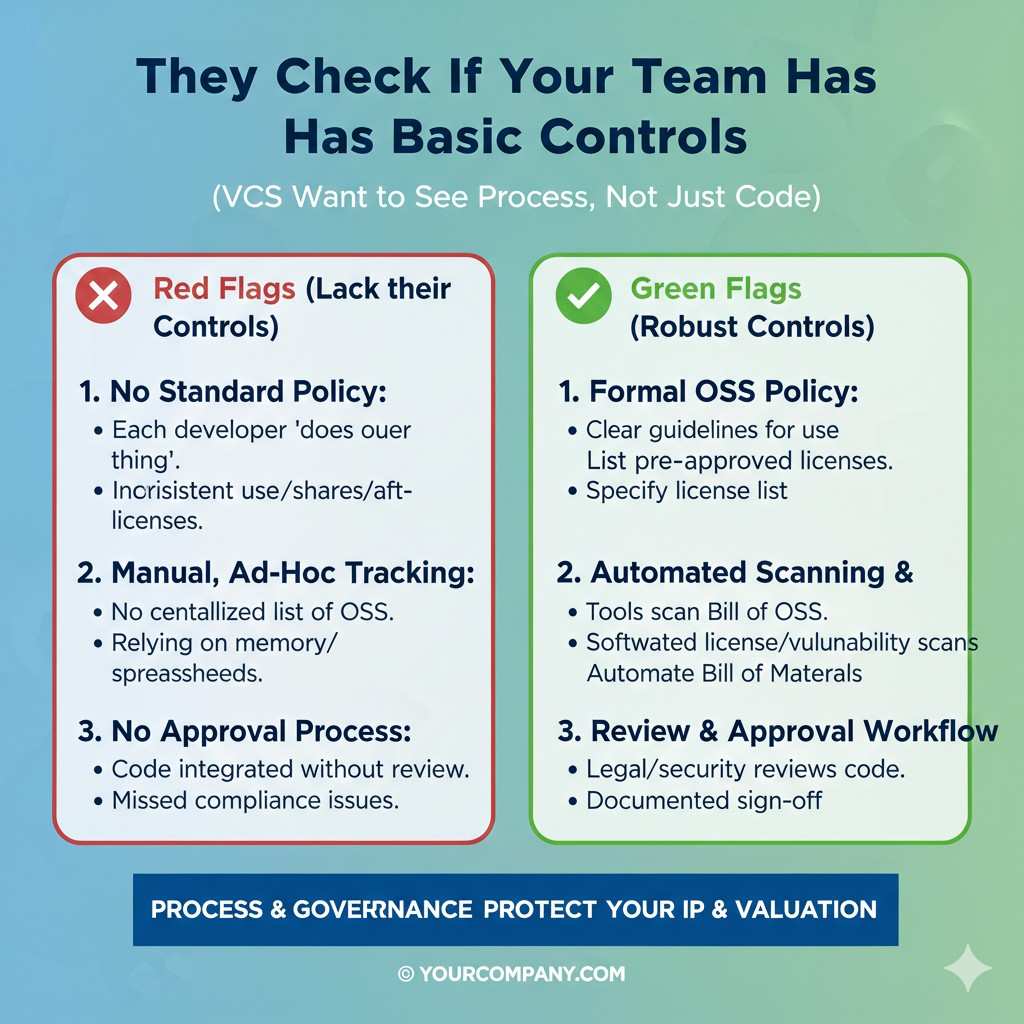
Most VCs do not expect an early startup to have a full legal department. But they do expect basic guardrails. They want to see that you do not merge unknown dependencies into production without review.
Even a simple process is a strong signal. A small checklist, a dependency scan in CI, and a shared file of approved licenses can go a long way.
The Real Problems That Delay Funding
Copied code with unclear origin
One of the fastest ways to scare an investor is code that looks copied from random sources without tracking. This includes snippets from GitHub gists, Stack Overflow answers, or older internal projects from past employers.
Even if the code is small, the origin matters. If you cannot prove you have the right to use it, the legal team treats it as a contamination risk. They do not want to fund a lawsuit.
“Copyleft” licenses in the core product

Some licenses require that if you distribute a combined work, you may need to share the source of certain parts. That can conflict with a closed commercial model, depending on how you ship and how you link.
This topic creates panic because founders often hear simplified advice like “GPL is bad.” The truth is more detailed. Risk depends on how you use the code, how you distribute, and whether your product is SaaS or shipped software.
But in diligence, nuance is hard. If the reviewer sees a risky license near core code, they might flag it and ask for a cleanup before funding.
Missing notices and attribution
Many permissive licenses are easy to comply with, but you still have to do the basics. You may need to include copyright notices, license texts, or attribution in your product distribution.
Startups skip this because it feels small. But diligence teams notice because missing notices signal that nobody is watching the details. The fix is usually simple, but it still creates delay.
Dependencies pulled through transitive chains
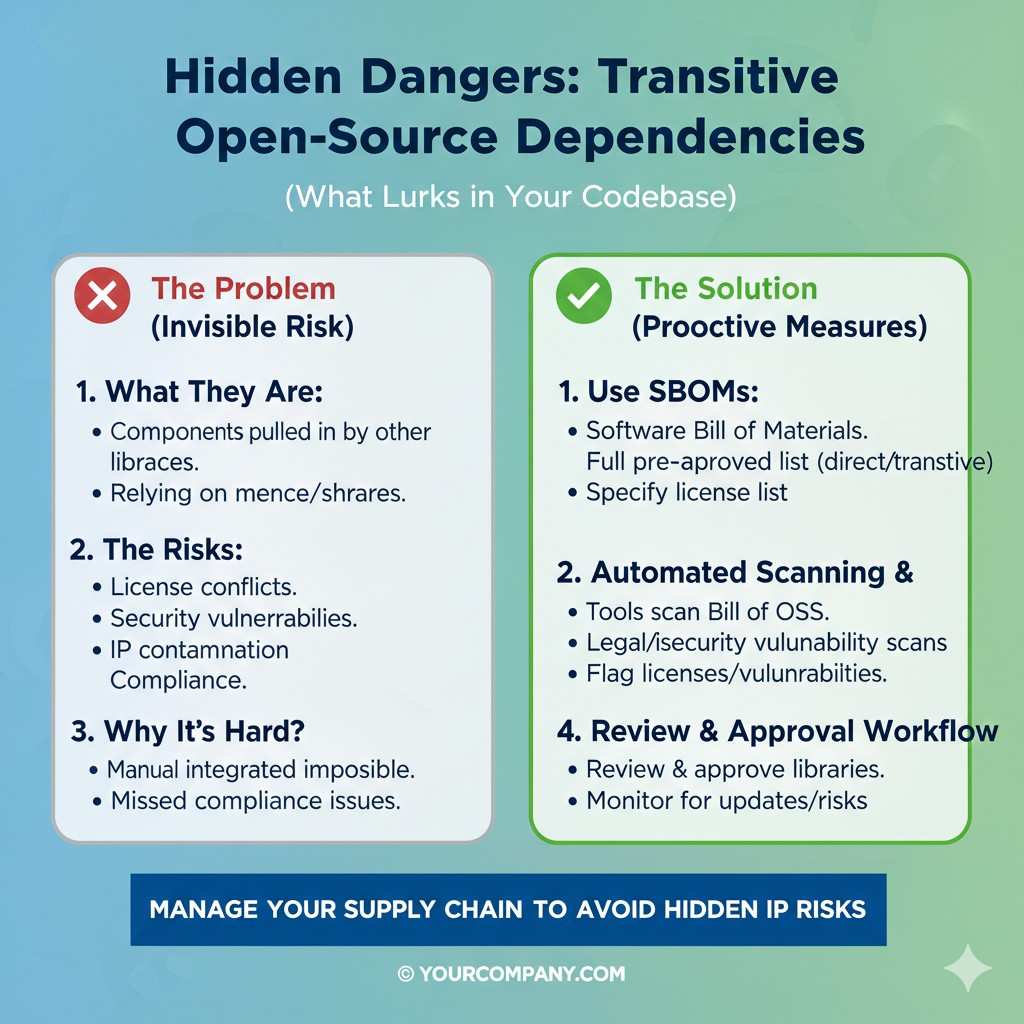
Even careful founders get surprised by transitive dependencies. You add one library, and it brings ten more. One of those may carry a license you would not have chosen.
This is why manual review alone is not enough. Without scanning tools, you often do not even know what you shipped.
If you want your IP story to be strong before diligence starts, Tran.vc helps you build defensible foundations early—so investors see a company that is serious from day one. Apply anytime: https://www.tran.vc/apply-now-form/
The Licenses VCs Pay Attention To
Permissive licenses are usually easy, but not “free”
MIT, BSD, and Apache 2.0 are popular because they usually allow commercial use with simple conditions. Those conditions still matter. You must keep notices, and in some cases include a copy of the license.
Apache 2.0 also includes patent-related terms that are important to understand. It is generally business-friendly, but you must follow the rules to avoid accidental non-compliance.
Strong copyleft licenses create diligence questions
Licenses like GPL are designed to keep software open under certain distribution conditions. Whether that impacts you depends on your architecture and distribution model.
If your product is a cloud service and you never distribute software, some obligations may not apply in the same way. But diligence teams do not want guesses. They want a clear explanation of your setup and why your use is safe.
Network copyleft can matter for SaaS
Some licenses are built with cloud delivery in mind. They can trigger obligations even when you provide software over a network rather than shipping binaries.
If your AI platform or robotics management console is delivered as a service, this category deserves special attention. Founders often overlook it because they assume “we do not distribute” means “we are safe.” That is not always true.
“Commons” and data licenses can trip AI teams
AI startups often pull datasets, model weights, and evaluation sets from public sources. Not all of those are “open source software licenses.” Some are data licenses with limits on commercial use, redistribution, or derivative works.
During diligence, this can be even more sensitive than code. If your model depends on data you cannot legally use in production, the risk is real. Investors will ask where your training data came from and what rights you have.
The Clean Story VCs Love to Hear
You know what is in the product
A clean story starts with a calm answer. You can say what dependencies you use, what licenses they carry, and how you track them.
You do not need to sound like a lawyer. You need to sound like a builder who keeps good records and takes ownership seriously.
You have a repeatable process
Investors like repeatable processes because they scale. If you can generate an SBOM in minutes, and if every new dependency goes through the same basic check, that is a strong signal.
The process does not need to be heavy. It only needs to be consistent. Consistency is what prevents surprises.
You built boundaries to protect your core IP
A strong story includes architecture choices that protect your core. Your secret sauce should not be a thin wrapper around a risky dependency.
When your core value is separated and clearly owned, you can file patents with confidence, license your product cleanly, and sign enterprise contracts without fear.
Tran.vc focuses on this exact foundation-building for deep tech teams—patent strategy, filings, and IP guidance as in-kind seed support. If you want help making your tech defensible early, apply here: https://www.tran.vc/apply-now-form/
The Tactical Setup You Can Do This Week
Start with a dependency inventory
You cannot manage what you cannot see. The first tactical move is to create a living inventory of what your product uses. This includes direct dependencies and the deeper ones that come along for the ride.
If your team already uses package managers like npm, pip, Maven, or Cargo, you have a starting point. The key is turning that into a clear list that also shows licenses.
Add license scanning to your build
Most founders wait until diligence to scan licenses. That is like waiting until tax day to start tracking expenses. It creates panic and rush decisions.
A scan in CI is calmer. It makes issues show up early, when fixes are cheap. It also creates a paper trail that shows you take compliance seriously.
Set a simple “new dependency” rule
You do not need a long policy. You need a rule that everyone follows. When a developer wants to add a new library, they should check license type and record it.
The point is not to block developers. The point is to prevent unknown code from slipping in without anyone noticing.
Track code origin for anything copied
If anyone copies code from outside sources, you need to record where it came from and what license applies. This includes snippets. This includes “temporary” code. Temporary code often becomes permanent.
If the origin is unclear, treat it as unsafe until proven otherwise. In diligence, “we are pretty sure” is not good enough.
Open Source Compliance for VC Due Diligence
How to Clean Up Before You Raise Money
Think like a buyer, not like a builder
When you are building, speed feels like the only goal. When you are raising, you are selling trust. Due diligence is the moment where investors try to see your company the way an acquirer or a large customer would see it.
That shift matters because open source issues often look small inside a sprint. But they look big in a legal review. The same dependency that felt harmless during a hack can become the reason a term sheet gets “paused.”
A good cleanup plan starts with one idea: remove surprises. You want to be able to say, with a straight face, that you know what is inside your product and you have the right to ship it.
Start by defining what “the product” is
Founders often scan the whole repo and then drown in noise. Instead, draw a clear circle around what investors will care about. That usually includes the code you ship to customers, the services that run production, the firmware you flash, and the libraries you bundle.
Internal prototypes and abandoned experiments matter less, unless they are still deployed somewhere. If a demo server is still online, it counts. If a robot in the field still runs an old build, it counts.
This step helps you stay focused. It also makes it easier to explain your system in diligence, because you are not mixing “real product” with “random side projects.”
Do one full scan and treat it like a baseline
Run your scanning tools once and save the results. Do not treat the first scan as a final report. Treat it like a baseline measurement.
The first time you scan, you will likely find weird things. Old packages, duplicate versions, forgotten dependencies, forks that nobody remembered. That is normal for early-stage teams.
What matters is what you do next. You take the baseline and turn it into a cleanup map with clear ownership. Not a long list of tasks, but a clear plan to remove the highest-risk issues first.
Handle the top risk items before you polish the rest
In diligence, not all issues are equal. A missing notice file is usually easy to fix. A copyleft license pulled into the heart of your proprietary code can be much harder.
Focus first on anything that touches your core value. If a dependency is in the part of the system that makes your company unique, you should treat it with extra care.
You are not doing this because open source is bad. You are doing it because your core is what investors are buying. That core needs clean ownership lines.
If you are building deep tech and you want help turning your core work into protectable assets early, Tran.vc can support you with IP strategy and patent services as in-kind seed funding. You can apply anytime here: https://www.tran.vc/apply-now-form/
How Investors Decide If a License Is “Risky”
The risk depends on how you ship
A license can be fine in one setup and risky in another. If you only use a library during internal development, the obligations may be minimal. If you ship it inside a device, obligations can increase fast.
Robotics teams often ship software in many forms at once. There is firmware on a robot, an edge agent, a cloud service, and a dashboard. Each layer can trigger different license concerns.
In diligence, investors want to know exactly how your system reaches users. “It runs in the cloud” is not enough if you also ship an on-prem package to a customer, or if you deliver containers that customers run.
Linking and combining is where lawyers focus
Founders often think, “We are not copying the code, we are just using it.” But some obligations depend on whether your code becomes a combined work with the open source component.
This is why architecture matters. If a component is used as a separate service with a clear interface, it may be easier to manage. If it is compiled directly into your binary, it can create a different set of questions.
You do not need to be a legal expert to handle this well. You need to be able to explain how the pieces connect and why your approach is safe.
Modifying open source creates extra duties
Using an open source library “as is” is one thing. Forking it and changing it is another. Once you modify, you may have obligations to document changes or share them, depending on the license.
Many startups fork because it is faster than waiting for upstream. That is understandable, but you must track it. In diligence, untracked forks look like hidden debt.
If you have forks, make a list. Note why they exist, what changes were made, and whether you plan to upstream those changes or keep them internal.
How to Build a VC-Ready “Open Source File” for Your Data Room
The goal is a calm, complete story
A data room does not need to be huge. It needs to answer questions without drama. When investors have to chase you for details, they feel friction.
A good open source file reads like a clear story. It says what you use, how you track it, and what you do to comply.
It also shows that you are not hiding anything. Transparency reduces fear.
Include an SBOM and explain how it was made
An SBOM is strongest when it is repeatable. Investors do not only want the list. They want to know the list can be regenerated and kept current.
When you share an SBOM, include a short note that says when it was generated and what it covers. For example, you can say it covers the production services and the shipped client code, and it excludes internal tooling.
This small context prevents confusion. It also signals you are thoughtful, not careless.
Add a simple license summary that maps to your product
Many diligence teams do not want to read raw tool output. They want a human summary of what matters.
A strong summary groups licenses by type and points out where each type appears. For example, you can explain that most dependencies are permissive and used in non-core areas, while core modules are company-owned and isolated.
You are not trying to “spin.” You are making the review easier. That alone can shorten diligence.
Provide your notice and attribution approach
If you ship software, you should have a clear way to include notices. This might be a NOTICE file, an About screen, a documentation page, or a folder in your distribution.
The exact format matters less than consistency. Investors want to see that you have a standard method and you follow it.
If you already have customers, this step also helps customer security reviews. Many enterprise procurement teams ask for the same compliance artifacts.
AI and Robotics: The Hidden Compliance Risk Is Often Data
Code is visible, data is sneaky
AI teams often focus on open source code and forget that training data can carry restrictions. This creates a nasty surprise because data issues can threaten your right to commercialize a model.
A dataset might be free to download but not free to use in a product. Some allow research but restrict commercial use. Some require attribution. Some restrict redistribution. Some limit what you can do with derived outputs.
In diligence, investors will ask where your data came from. If you answer with vague phrases like “public data” or “open data,” you may trigger deeper scrutiny.
Model weights and checkpoints need tracking
More teams are using pre-trained models as a base. That can be smart, but weights are not always licensed the same way as code.
A model might be published under a license with usage restrictions. Some have limits around certain fields, certain user groups, or commercial use. Some require that you pass along terms to your users.
You do not want to discover those restrictions after you have built a product around the model. That is why you should track model sources and licenses the same way you track code dependencies.
Your pipeline matters as much as your dataset
A compliance story is stronger when you can describe your data pipeline clearly. Investors care about whether your training process can be repeated and audited.
If you can show that your datasets are sourced, recorded, and permissioned, you look mature. If your data is a folder named “final_final_v3,” you look risky.
This is not about being perfect. It is about being clean enough that smart people can trust you.
Tran.vc works with technical founders to build defensible foundations early. If your AI or robotics system is new and you want to protect the core through smart IP strategy and patents, you can apply anytime here: https://www.tran.vc/apply-now-form/
How to Fix Common Problems Without Slowing Engineering
Replace risky dependencies with safer options
If a library’s license creates questions, the cleanest fix is often replacement. This is not always easy, but it is often easier than trying to argue about edge cases during diligence.
The key is to replace early. Replacing a core dependency two weeks before closing a round is painful. Replacing it months earlier is manageable.
When you evaluate replacements, you should consider not only features, but also maintenance health. Investors dislike dependencies that are abandoned, even if the license is fine.
Isolate components to reduce “license spread”
Sometimes you cannot replace a dependency because it is deeply useful. In that case, isolation can help.
If you keep that component as a separate service or module with clean boundaries, you can often reduce uncertainty. You can also make it easier to document how the component is used.
This is especially relevant in robotics stacks where real-time components and safety-critical modules should be tightly controlled. Keeping open source parts separated from proprietary control logic can strengthen your story.
Document forks and plan your path
If you maintain forks, the worst move is pretending they do not exist. The best move is to document them and show you have a plan.
A plan can be simple. You can say you forked to fix a bug, you track your changes, and you will either upstream them or keep the fork internal without distribution. The details matter, but the clarity matters more.
In diligence, “we have a list and a plan” beats “we think it is fine.”
