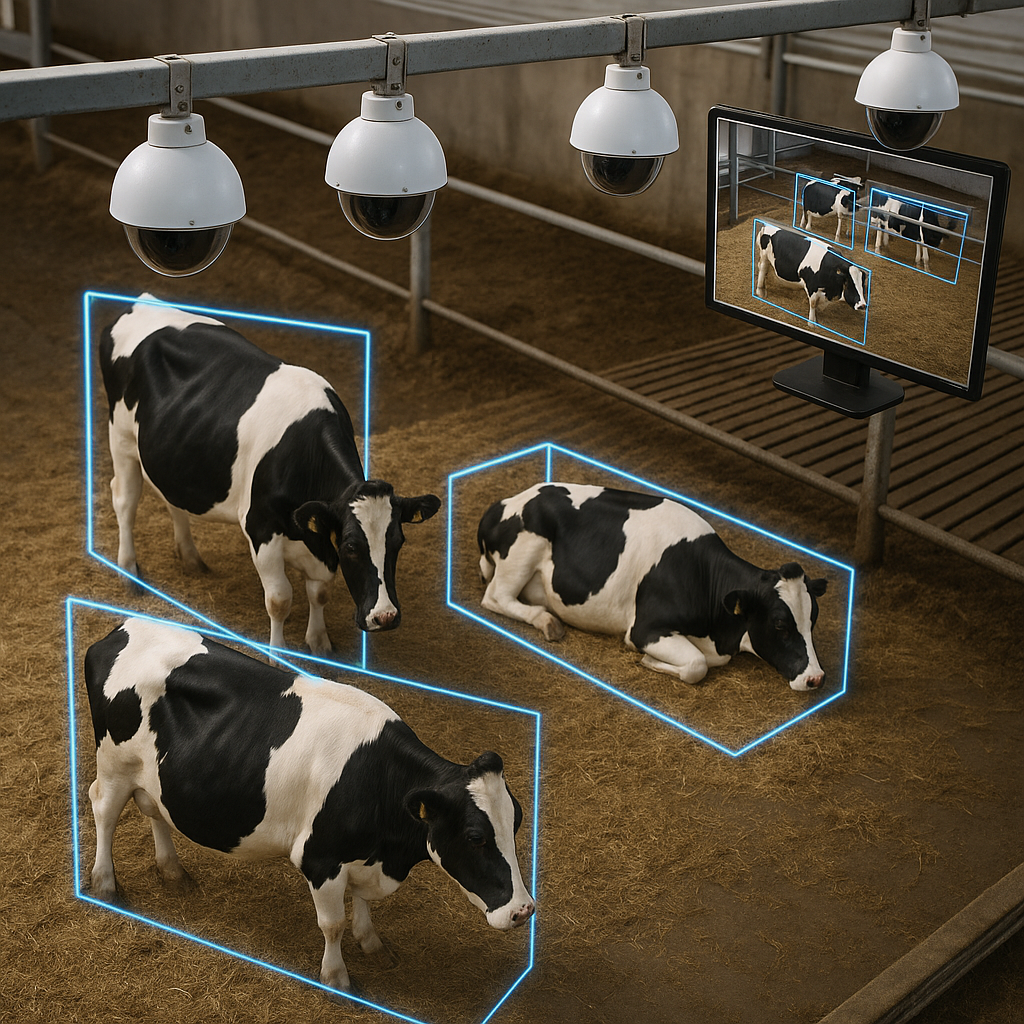
ANIMAL HUSBANDRY SYSTEM
Invented by LI; Yan, VAN ADRICHEM; Paulus Jacobus Maria, ANIRAJ; Ananthu, VAN VLIET; Sjoerd Timo, SOZEN; Cagla, VAN DER SLUIS; Joram Robin, LELY PATENT N.V. Modern animal husbandry is all about keeping animals healthy and comfortable. But tracking animals as they move around a barn or field is tough. This new patent application introduces a […]
ANIMAL HUSBANDRY SYSTEM Read More »